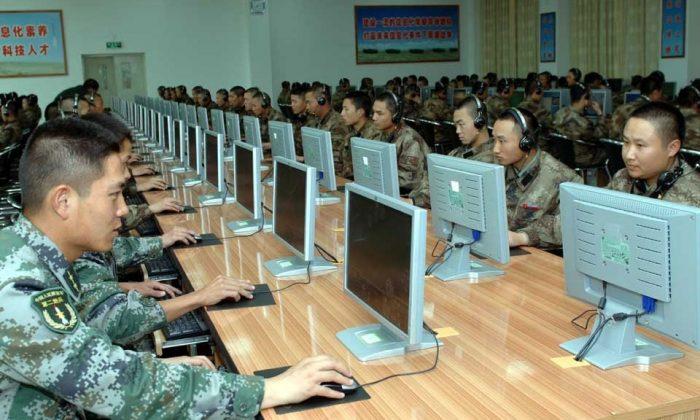
With a hope to end the onslaught of Chinese cyberattacks on U.S. businesses, President Barack Obama announced a deal with the leader of the Chinese Communist Party (CCP), Xi Jinping, on Sept. 25, 2015, to end cyberattacks meant for economic gain.
The next day, the Chinese cyberattacks on U.S. businesses continued as usual.
The impact of Chinese economic theft was the focus of a new segment on “60 Minutes,” which aired Jan. 17. It highlighted an environment where Americans are being spied on by a foreign government, and where U.S. CEOs are doing business with China while knowing they have only five or six years to do business before their products are stolen.
“The CEO knows that by going into business with China, he is committing long-term suicide,” said Richard Bonin, who produced the story for “60 Minutes,” in a CBS News video.
What was probably most interesting was that despite the noise around Chinese economic theft, there is an air of quiet tolerance among businesses, with government procurement, and with international regulation.
If the cyber agreement between the United States and China has shown us anything, it’s that the CCP will not cooperate when it comes to stopping economic theft. For them, the risk of these attacks is negligible, the benefits of the attacks are too great, and the Chinese economy has come to rely too heavily on theft to just switch it off.
One of the key problems is that the United States still doesn’t have a real strategy for dealing with cyberattacks. This issue was highlighted by Gen. Michael Hayden, the former director of the NSA and CIA, during a recent speech at the S4x16 ICS/SCADA cybersecurity conference in Miami.
“We lack a legal policy framework,” Hayden said, according to cybersecurity news website Dark Reading. He added, “People ask how come government isn’t doing something about it … Government will be permanently late to the need in providing cybersecurity.”
This ties back to the cybersecurity agreement with China. One of the key problems with cybersecurity, in general, is that the United States has not yet demonstrated that using cyberattacks for economic gain is a risky endeavor.
Cyberattacks are often carried out from countries that have no extradition treaties with the United States, U.S. businesses are not allowed to launch counterattacks, and the business environment often has CEOs petrified of making the attacks public for fear of lawsuits and angry investors.
It’s a crime with high profit and little risk, and as the “60 Minutes” segment highlighted, even businesses with alleged stolen products are still able to sell these products freely in the United States.
Daniel McGahn, the head of American Superconductor, spoke about his experience of having his software stolen in China. He said in the “60 Minutes” segment that he had to then fire 600 of his nearly 900 employees, and his company lost “well over a billion dollars.”
Sinovel, the company partly owned by the Chinese regime that allegedly robbed him, now exports wind turbines running on his technology. They were even able to sell one of these turbines to the state of Massachusetts, which was paid for with federal stimulus funds.
The case is a clear example of what a cyber agreement with China needs, yet still lacks: sanctions that can discourage theft.
Obama signed an executive order giving himself the ability to sanction companies that commit economic theft, and the threat of sanctions was believed to be one of the key tools used to nail down the cyber agreement in September. But as I reported at the time, the sanctions were not mentioned directly in the agreement.
In other words, the cyber agreement lacks teeth. It still gives the Chinese regime no real reason to stop its attacks—and instead just gave it a platform of dialogue where it can continue pretending it has no part in the problem.
The other key problem is also one I’ve mentioned before. Economic theft is not just a cyber problem, and the Chinese regime—in particular—still uses a large number of conventional spies to carry out its work.
This was also highlighted in the “60 Minutes” segment, with American Superconductor.
McGahn noted in the segment that when he started doing business with China, he made sure his systems were locked tight. They used strong encryption and had a solid system for cybersecurity.
Then, in 2011, they tested their software on Sinovel’s turbines. The system had been programmed to shut down after the test, but the blades kept spinning. The Chinese company had successfully broken his encryption.
It turned out the breach took place through one of their employees—an Austrian named Dejan Karabasevic, who would later spend a year in jail for his crime. McGahn said the Chinese regime “offered him women. They offered him an apartment. They offered him money. They offered him a new life.”
And all it took for McGahn’s company to lose its key product to China, was for Karabasevic to say “yes.”
The problem of economic theft seems complicated on the surface, but when you boil it down, it’s pretty simple: the Chinese regime and its state-run companies will use any means they have to steal U.S. intellectual property, and gradually push U.S. companies out of the global market.
To solve the problem, the United States needs to broaden its view of economic theft past cybersecurity. And it needs to find a solution that turns what is currently a highly profitable, and generally safe, operation into something that isn’t worth the risk.