NEW YORK—It is the first comprehensive study of its kind and its timing could not be better. It is an analysis of the tools used by people living in repressive regimes to get past Internet censors, and what users who rely on them daily experience.
Around 400 users of Internet circumvention tools living in China, Iran, Burma, and Azerbaijan were surveyed by the nonprofit Freedom House on which of 14 tools they used and why. Two years in planning, and one year in the making, the report comes out at a time when the Internet was used by protesters in the Middle East to organize and overthrow repressive governments.
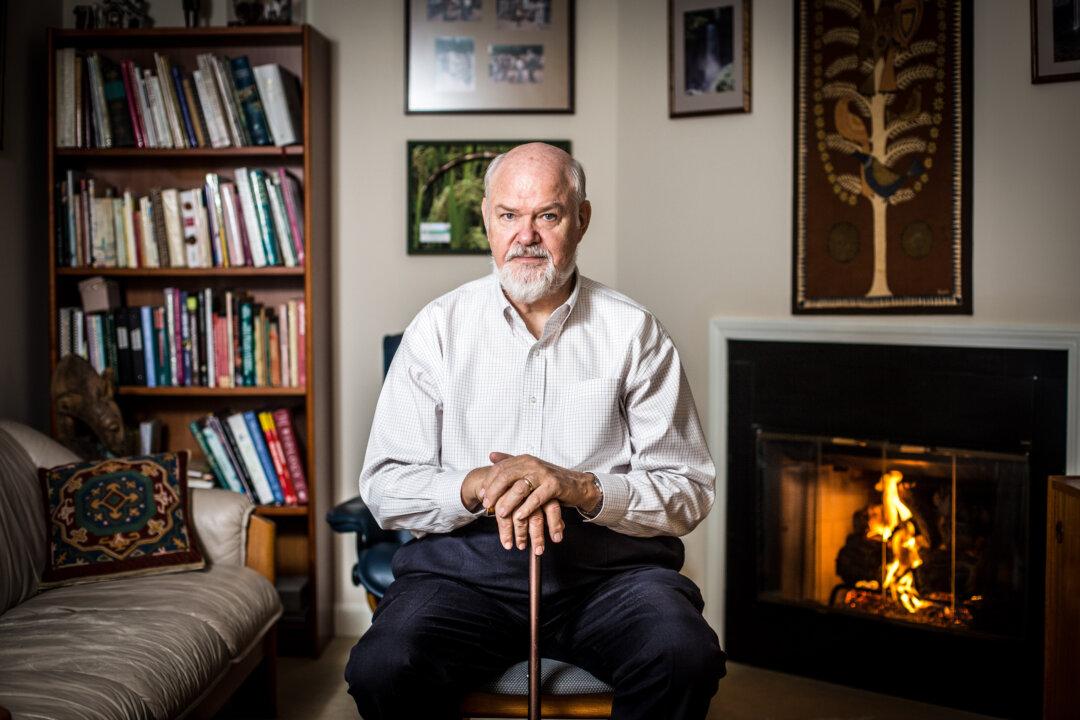
“There is a moment in time—so it is all the more relevant now, and that is that the larger Internet freedom space be supported,” said Robert Guerra, one of the report authors, and head of the Global Internet Freedom Initiative at Freedom House.
The report found that all of the tools included in the report were used regularly in the four countries. Certain tools stood out in specific countries more than others.
Overall, researchers were surprised to learn that users cared more about speed than about personal security. They identified the need for more education of Internet users about the dangers of external threats like malware that can be used by government censors to invade a home computer and collect information about illegal Internet use.
“In most cases they make a big cheer when they get a successful access and they forget about the knock at the door (that comes later),” said Cormac Callanan, another of the report’s authors, and the director of Aconite Internet Solutions, as well as a policy consultant on international computer networks.
It could be that tools like Freegate, Ultra Surf, or even Google Reader Cache are primarily designed for, and are very effective at, allowing users to bypass government censors and get online. Some of the tools offer encryption technologies, but generally they are not designed to hide Internet activity once the firewall has been breached.
The report includes a flowchart to help Internet users living under repressive regimes determine which tools would work best based on the criteria of speed, security, privacy, and whether or not users wish to share information online with others (versus simply accessing Web pages).
Authors of the report distinguish between types of users, indicating that those who simply want to access information may be less subject to risk than those who are downloading and sending materials over the Web.
The report recommends that “keen political activists ... not compromise on the security of communications.”
Guerra said it is important for users to educate themselves about how to stay safe. He recommends that they learn how to check for viruses and malware, and use passwords to protect their computers.
“Particularly, the at-risk individuals need to employ a variety of different tools,” Guerra said.
The report was funded by the Bureau of Democracy, Human Rights, and Labor (DRL), a branch of the U.S. Department of State.
DRL has received millions of dollars in funding from Congress over the past few years. Stakeholders have been giving input and awaiting a plan for how the money will be spent.
Guerra suggested that besides specific funding for Internet circumvention tools, it is likely that DRL will fund projects involving cell phone security, personal privacy, and cybersecurity protections.
Around 400 users of Internet circumvention tools living in China, Iran, Burma, and Azerbaijan were surveyed by the nonprofit Freedom House on which of 14 tools they used and why. Two years in planning, and one year in the making, the report comes out at a time when the Internet was used by protesters in the Middle East to organize and overthrow repressive governments.
“There is a moment in time—so it is all the more relevant now, and that is that the larger Internet freedom space be supported,” said Robert Guerra, one of the report authors, and head of the Global Internet Freedom Initiative at Freedom House.
The report found that all of the tools included in the report were used regularly in the four countries. Certain tools stood out in specific countries more than others.
Overall, researchers were surprised to learn that users cared more about speed than about personal security. They identified the need for more education of Internet users about the dangers of external threats like malware that can be used by government censors to invade a home computer and collect information about illegal Internet use.
“In most cases they make a big cheer when they get a successful access and they forget about the knock at the door (that comes later),” said Cormac Callanan, another of the report’s authors, and the director of Aconite Internet Solutions, as well as a policy consultant on international computer networks.
It could be that tools like Freegate, Ultra Surf, or even Google Reader Cache are primarily designed for, and are very effective at, allowing users to bypass government censors and get online. Some of the tools offer encryption technologies, but generally they are not designed to hide Internet activity once the firewall has been breached.
The report includes a flowchart to help Internet users living under repressive regimes determine which tools would work best based on the criteria of speed, security, privacy, and whether or not users wish to share information online with others (versus simply accessing Web pages).
Authors of the report distinguish between types of users, indicating that those who simply want to access information may be less subject to risk than those who are downloading and sending materials over the Web.
The report recommends that “keen political activists ... not compromise on the security of communications.”
Guerra said it is important for users to educate themselves about how to stay safe. He recommends that they learn how to check for viruses and malware, and use passwords to protect their computers.
“Particularly, the at-risk individuals need to employ a variety of different tools,” Guerra said.
The report was funded by the Bureau of Democracy, Human Rights, and Labor (DRL), a branch of the U.S. Department of State.
DRL has received millions of dollars in funding from Congress over the past few years. Stakeholders have been giving input and awaiting a plan for how the money will be spent.
Guerra suggested that besides specific funding for Internet circumvention tools, it is likely that DRL will fund projects involving cell phone security, personal privacy, and cybersecurity protections.