Two Chinese researchers with alleged ties to the Chinese military have been arrested on federal charges while attempting to board China-bound flights, according to separate criminal complaints unsealed on Aug. 28.
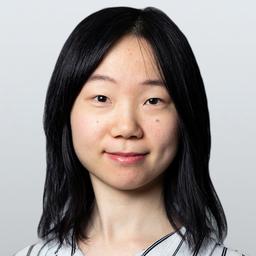
One of the arrested was Guan Lei, a 29-year-old researcher at the University of California, Los Angeles (UCLA), who was charged with destroying evidence to obstruct an investigation by the Federal Bureau of Investigation (FBI) into whether he had transferred sensitive U.S. software or data to China, the Justice Department said.