SPECIAL COVERAGE
Read More
Read More
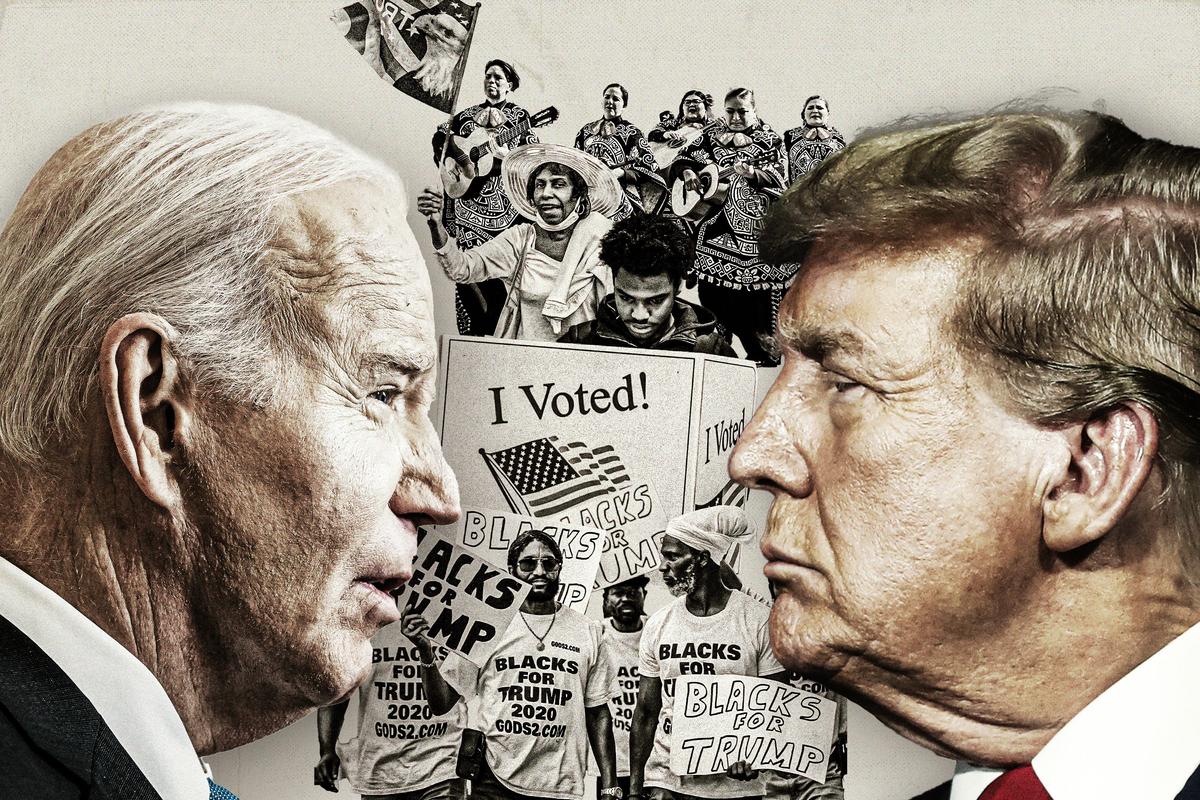
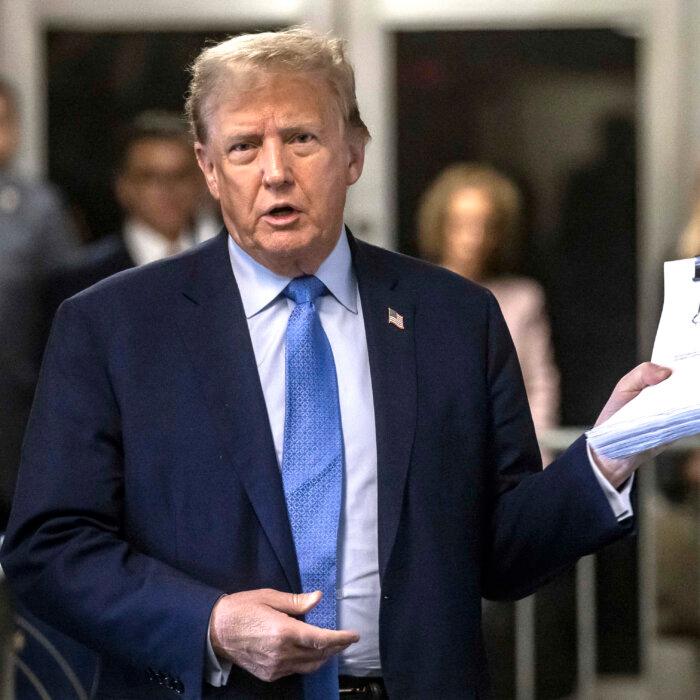
Trump Says He'll Wait at Courthouse If Biden Will Come Debate
President Biden had said he would be “happy to debate” Trump before November, and Trump responded on social media.
Trump Says He'll Wait at Courthouse If Biden Will Come Debate
President Biden had said he would be “happy to debate” Trump before November, and Trump responded on social media.
Top Premium Reads
Top Stories
Most Read
Indo-Pacific Bill Could Allow Biden to Send More Weapons to Israel, Ukraine: Lawmakers
‘If the money were truly intended for Taiwan, Congress could directly appropriate it as such,’ said Rep. Harriet Hageman.
Can California Cities Clear Homeless Camps? Depends on Supreme Court Ruling
Justices heard arguments that laws against camping violate the Constitution’s ban on ‘cruel and unusual’ punishment. Cities hope for clarity.
Group Issues Major Warning on Federal Agency’s Proposed Tax Increase
A policy group this week warned that the U.S. Department of Treasury’s proposed budget could significant increase taxes for certain Americans.
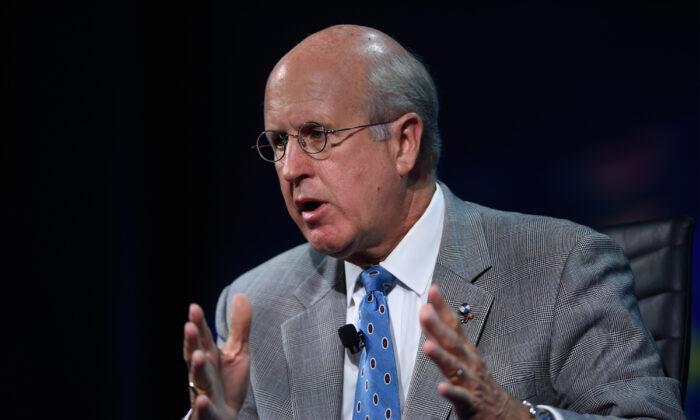
Washington’s Fiscal Mess Is Irresponsible, Unethical, Immoral: Former US Comptroller General
‘We’ve lost our sense of stewardship,’ David Walker said.
Blinken Meets CCP Leader Xi, Questions China’s Support for Russia’s War
Talks with the Chinese sides were ‘candid’ and ‘constructive,’ Mr. Blinken said at a press conference as he wrapped up his visit on April 26.
Fed’s Preferred Inflation Measure Rose More Than Expected
Next inflation stop will be the consumer price index.
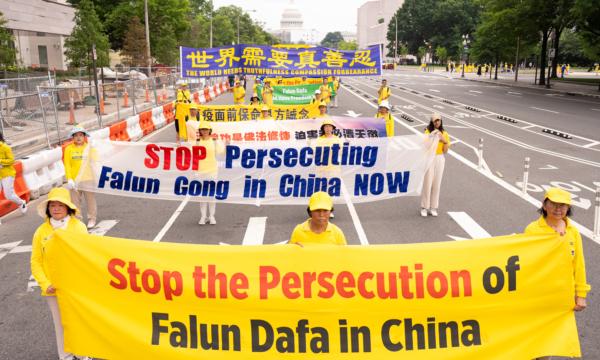
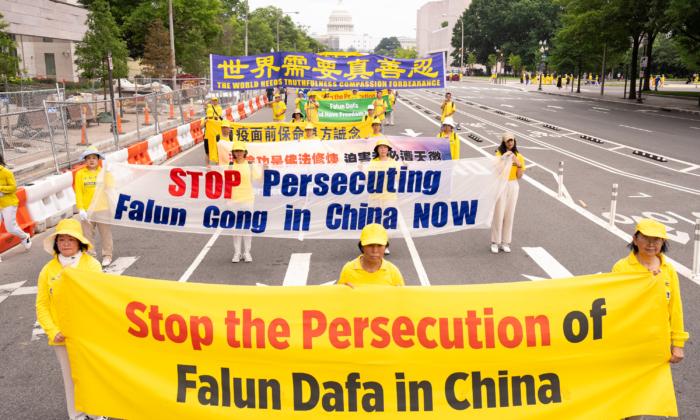
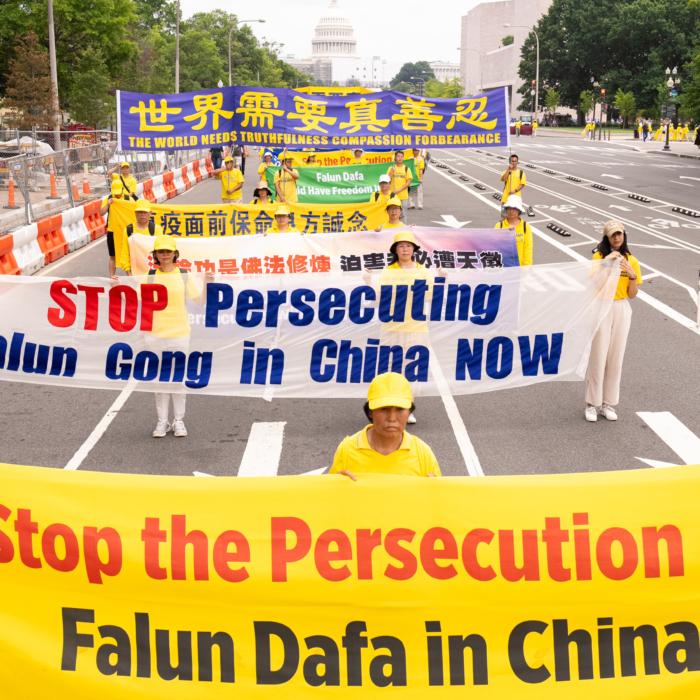
Congressional Commission Demands CCP End Decades-Long Persecution of Falun Gong
Less than three months after the appeal, on July 20, 1999, the Chinese Communist Party launched the brutal persecution of Falun Gong adherents across China.
Planes Almost Collide at 2 Major Airports as Boeing Probe Advances
Some aviation experts argue the FAA’s focus on ‘diversity’ instead of ’merit' in hiring pilots and controllers is leading to serious safety concerns.
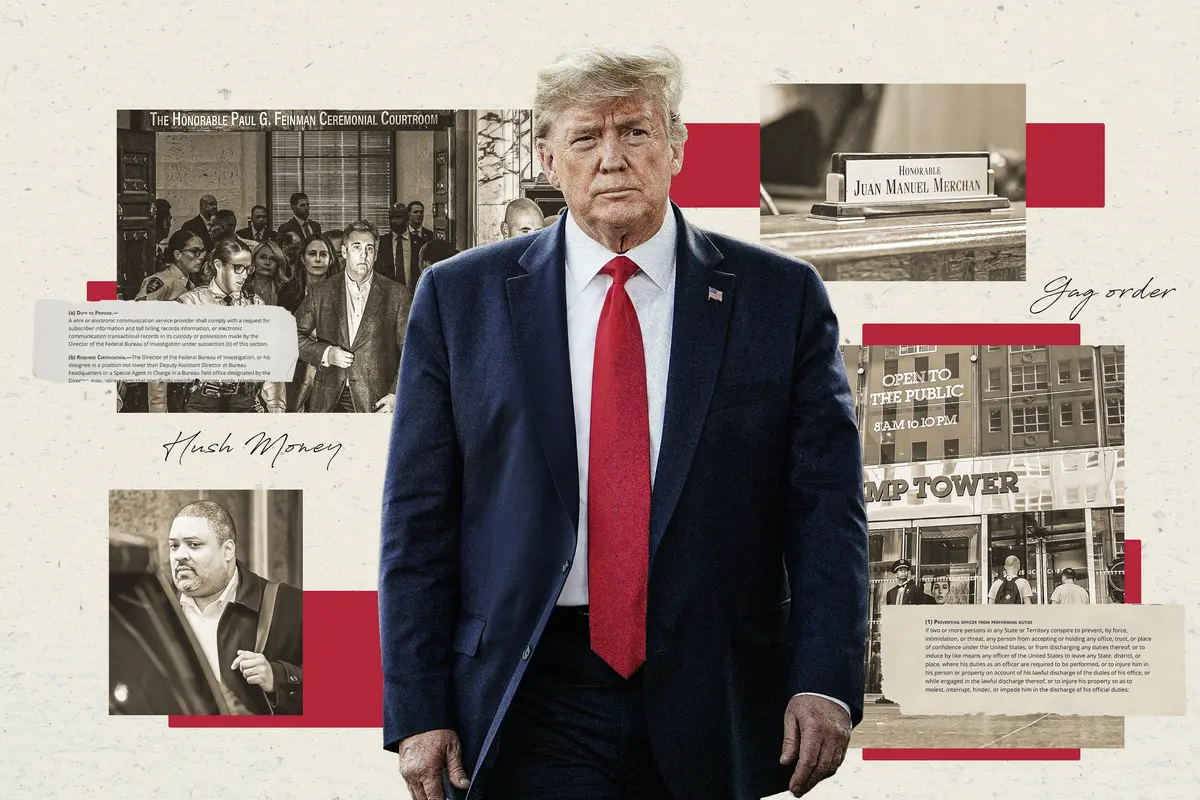
Manhattan DA Accused of Politically Motivated Prosecution in Trump Trial: House Report
‘Bragg’s politically motivated prosecution of President Trump threatens to destroy this notion of blind justice,’ the committee alleges.
Editors' Picks
Supreme Court Seems Open to Allowing Some Presidential Immunity, May Delay Trump Trial
Justices wrestled with how to define a president’s ‘official’ versus ‘private’ acts. A decision may delay President Trump’s trial, which would hand him a win.
Pentagon Moving Ahead With Plans to Pull US Troops From Niger, Draw Down in Chad
While working to expel Western forces that have previously been stationed in the country, Niger’s junta government has begun to form partnerships with Russia.
Key Witness Lays Out Saga of Deals Comprising Alleged Conspiracy in ‘Breathtaking’ Trump Trial Testimony
‘Breathtaking and amazing testimony,’ Former President Donald Trump told the press, noting that it ‘was really an incredible, an incredible day.’
Supreme Court Likely to Send Trump Immunity Case Back to District Court: Experts
The case could affect Trump’s other trials and set a long-lasting precedent for future administrations.
The ‘Fast and Furious’ Actor Who Left Hollywood for a Traditional Lifestyle
Lucas Black, who stars in the new film ‘Unsung Hero,’ takes his sons fishing and hunting, while instilling in them confidence and a sense of responsibility.
The ‘Fast and Furious’ Actor Who Left Hollywood for a Traditional Lifestyle
Lucas Black, who stars in the new film ‘Unsung Hero,’ takes his sons fishing and hunting, while instilling in them confidence and a sense of responsibility.
Epoch Readers’ Stories
A History Of The American Nation
A patriotic poem by Ted Schneider
Of Cars and Kids
Why should our kids have to settle for a Trabant, or a Pyonghwa, education when they could have a BMW?
A Nation Divided
Poem by an American Patriot
What Is Going on Here?
There are two major things plants need to survive and continue generating our life saving oxygen. The first is CO2, and the second is sunshine.
Inspired Stories
Empower the World with Your Story: Share Love, Inspiration, and Hope with Millions
Special Coverage
Special Coverage

Cultivate a Positive Mindset
This one change makes you kinder, improves relationships, boosts playfulness and joy, and makes you more goal focused.

Cultivate a Positive Mindset
This one change makes you kinder, improves relationships, boosts playfulness and joy, and makes you more goal focused.
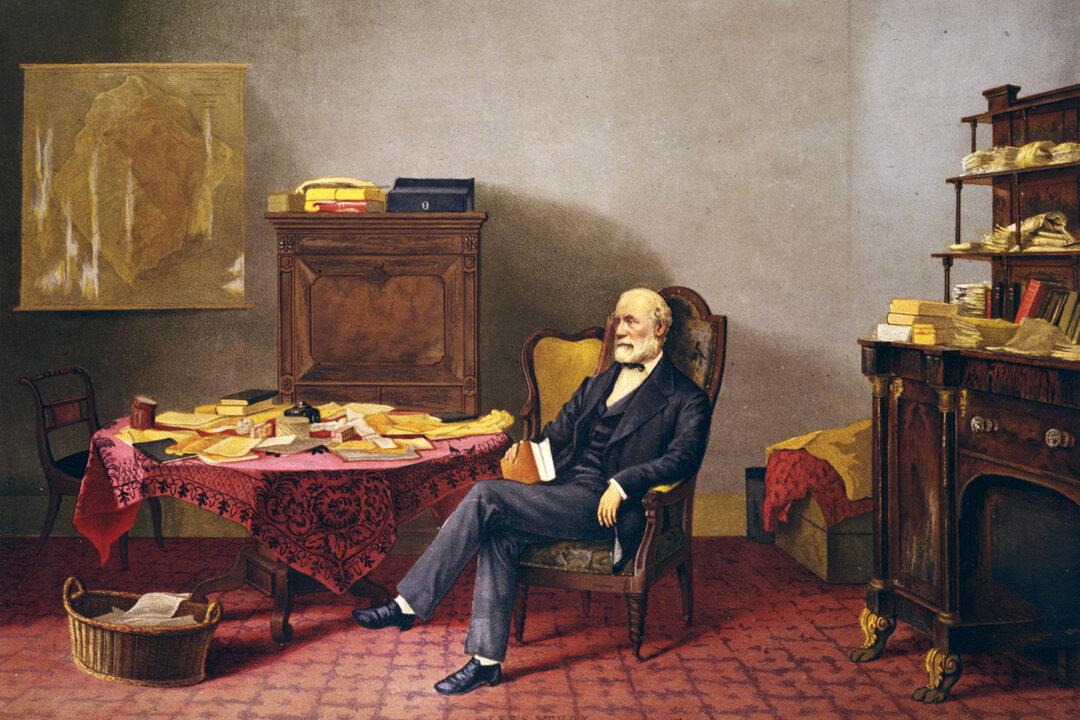
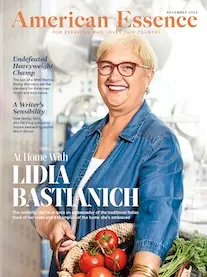
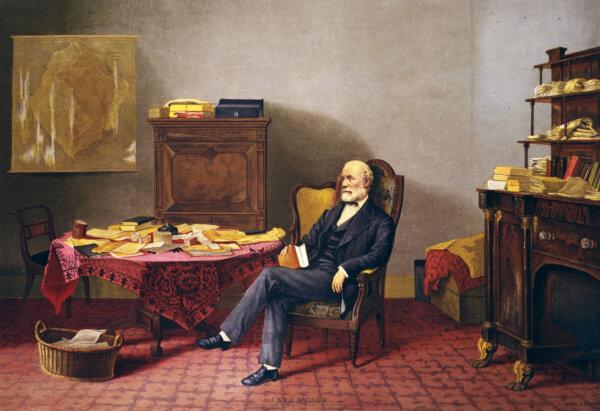
The Two Reputations of Robert E. Lee
While those in the past saw Lee’s stellar qualities, today, some cannot see that he was a man defined, like all of us, by his time.
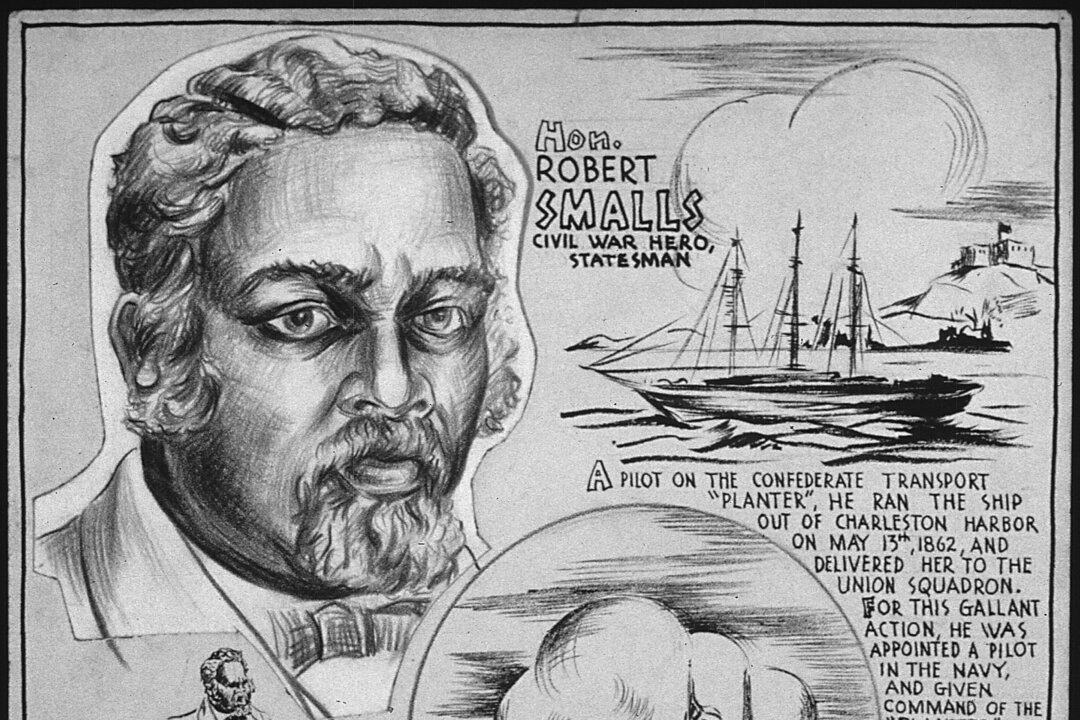
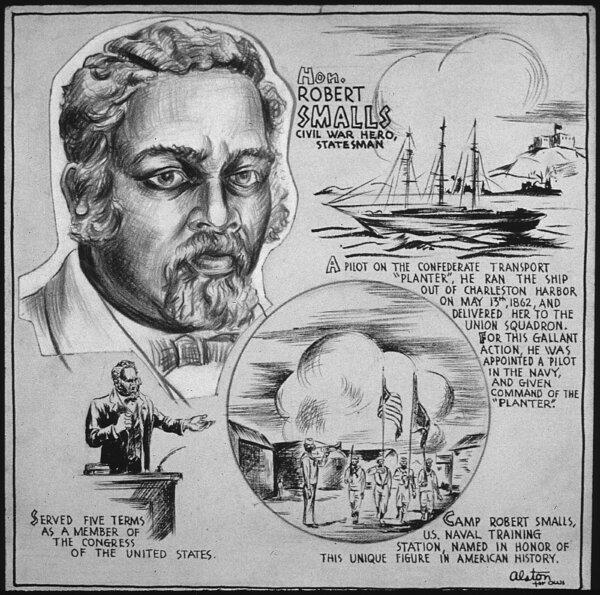
Robert Smalls: Navy Captain and Reconstruction-Era Politician
This former slave would not let anything stop him on the road to freedom.

US Shoppers Buy Less Bread in Bad News for Farmers
Cookie and cracker unit sales were down 3.4 percent from the previous year and grocery-aisle bread sales fell two percent.

Michigan Lawmakers Try to Put Brakes on Mackinac Island’s E-bike Riders
Mackinac Island doesn’t have cars but the speed of e-bikes are becoming a problem.

Taking the Kids: To the Smithsonian Museums
The Smithsonian Institution is the world’s largest museum, education and research complex.

Airbnb Rentals Could Be Harder to Come by in Hawaii. Here’s Why and When That Might Happen
New bills will give counties the power to limit short-term rentals amidst housing shortages.
Michigan Lawmakers Try to Put Brakes on Mackinac Island’s E-bike Riders
Mackinac Island doesn’t have cars but the speed of e-bikes are becoming a problem.