SPECIAL COVERAGE
Read More
Read More
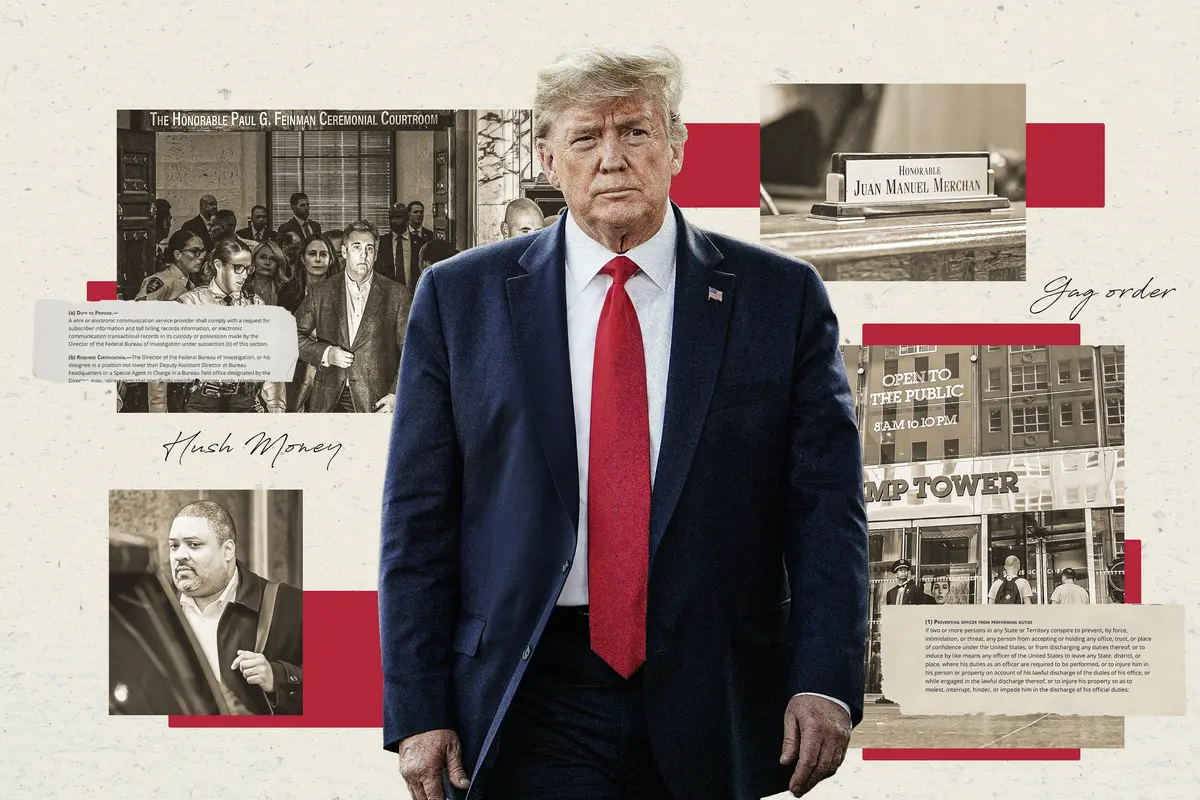
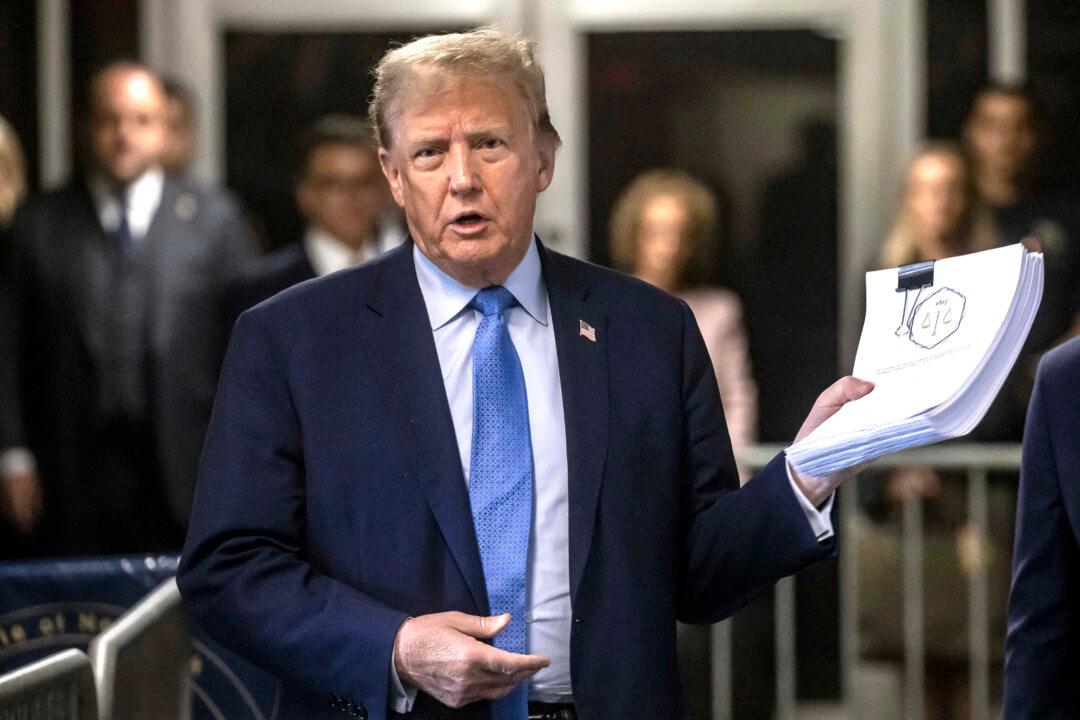
Key Takeaways From Week 2 of Trump Trial in New York
Trump has been charged with 34 counts of falsifying business records.
Key Takeaways From Week 2 of Trump Trial in New York
Trump has been charged with 34 counts of falsifying business records.
Top Premium Reads
Top Stories
Most Read
What’s Next in Congress After Passage of Foreign Aid Package
The House is scheduled to take up several bills, with the most notable being legislation to combat anti-Semitism on college and university campuses.
Names of 5 Additional Defendants Revealed In Arizona’s ‘Fake Electoral’ Case
Arizona Republicans released a statement denouncing the charges as ’suspiciously convenient and politically motivated' given their timing.
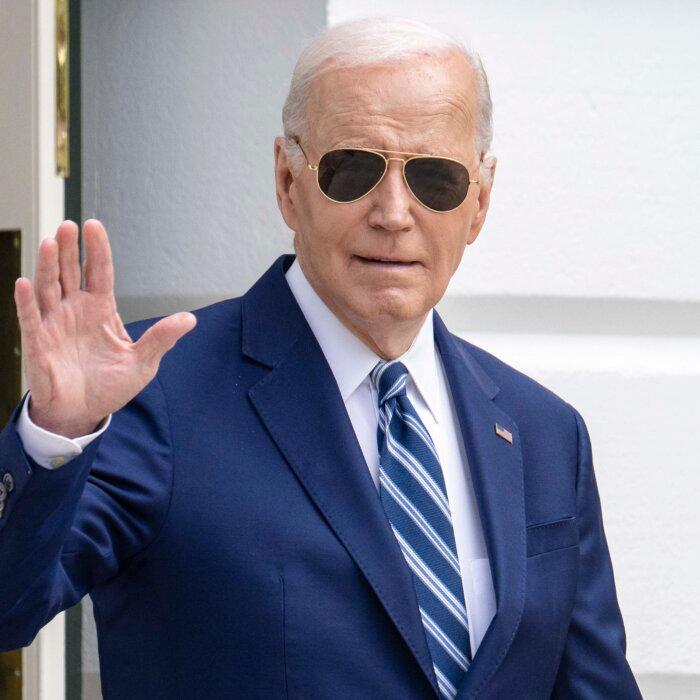
Biden Admin Announces $6 Billion in New Security Funding for Ukraine
The security package includes Patriot missiles, High Mobility Artillery Rocket Systems (HIMARS), and 155mm artillery rounds among other things.
Biden Administration Delays Decision on Menthol Cigarette Ban
Roughly 81 percent of black adults who smoke cigarettes use menthol varieties, according to the U.S. Centers for Disease Control and Prevention.
Suppression of Faith Has Backfired on CCP: Researcher
‘Even with all this brutality, even with all the billions of dollars, the CCP hasn’t been able to’ change people’s beliefs, said China expert Sarah Cook.
Second Witness in Trump ‘Hush-Money’ Case Called by Prosecutors
Former Trump assistant Rhona Graff testified on Friday.
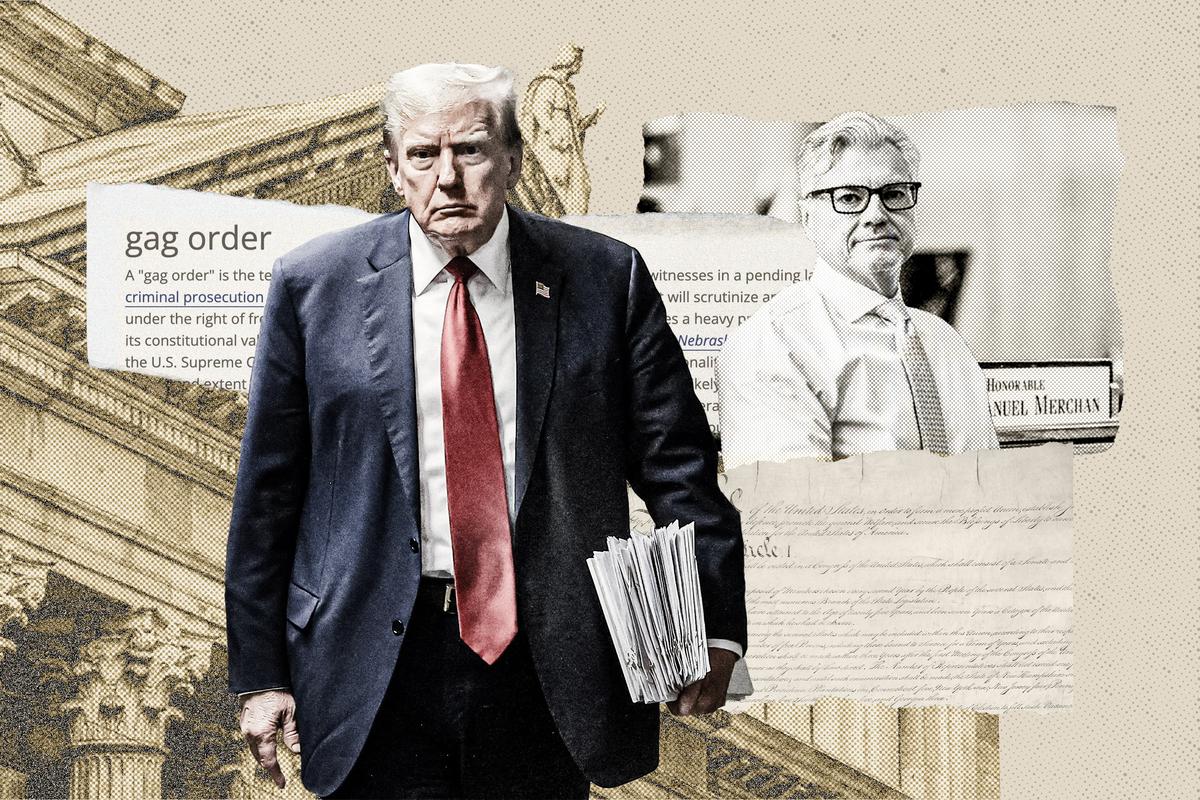
Judge Merchan Threatens Trump With ‘Immediate Arrest and Imprisonment’ Over Gag Order Violations
‘Warning: your failure to appear in court may result in your immediate arrest and imprisonment for contempt of court,’ the judge wrote in his order.
Scenes From Chaos: A Journalist Recounts Her Escape From Kabul
Indian journalist Nayanima Basu recalls a harrowing adventure in her newly-released book.
NYC Councilman on Israel–Palestinian Campus Protests: I Never Dreamed There‘d Be a US ’Movement to Back Terrorists’
‘Many of them are products of our universities. And that’s, that’s distressing, to say the least,’ said Democrat New York City Councilman Robert Holden.
Editors' Picks
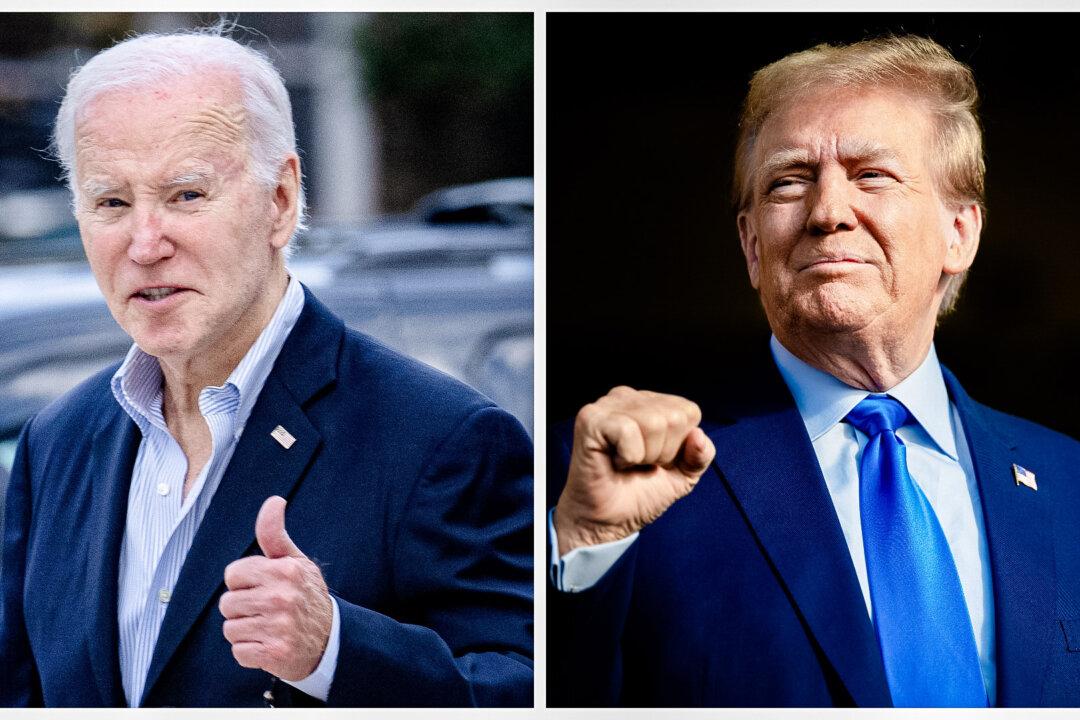
Supreme Court Seems Open to Allowing Some Presidential Immunity, May Delay Trump Trial
Justices wrestled with how to define a president’s ‘official’ versus ‘private’ acts. A decision may delay President Trump’s trial, which would hand him a win.
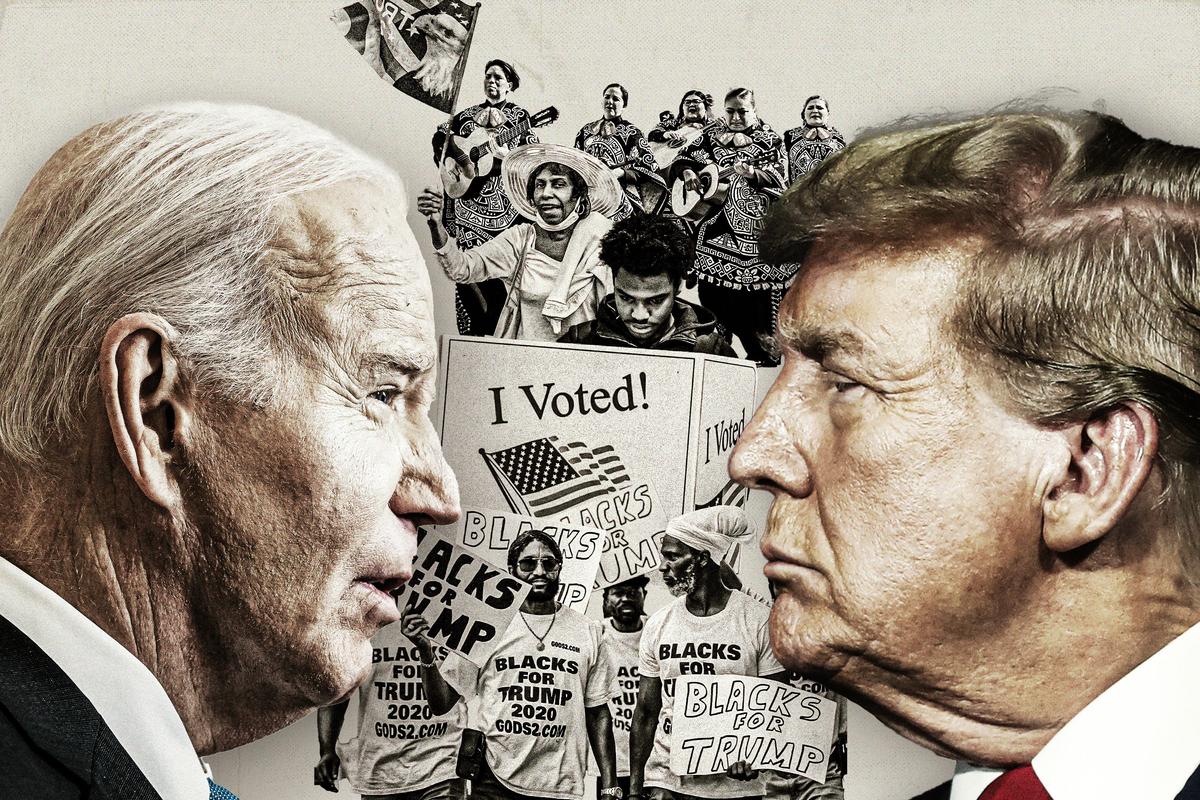
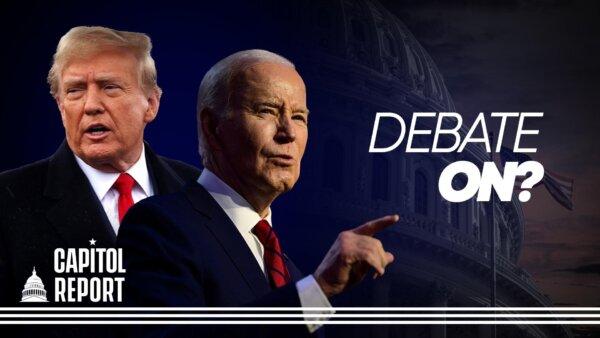
Biden Says He’s ‘Happy’ to Debate Trump
Trump has repeatedly called on the president to debate him.
Indo-Pacific Bill Could Allow Biden to Send More Weapons to Israel, Ukraine: Lawmakers
‘If the money were truly intended for Taiwan, Congress could directly appropriate it as such,’ said Rep. Harriet Hageman.
It’s Not Clear If Jack Smith’s Trump Case Will Go to Trial Before Election, Analysts Say
Several legal experts reacted to the Supreme Court’s hearing on Thursday.

Fresh, Healthy Spring Rolls Are a Project Worth the Effort
But for the time-strapped (or lazy) home cook, there’s also a way to a quicker fix.
Fresh, Healthy Spring Rolls Are a Project Worth the Effort
But for the time-strapped (or lazy) home cook, there’s also a way to a quicker fix.
Epoch Readers’ Stories
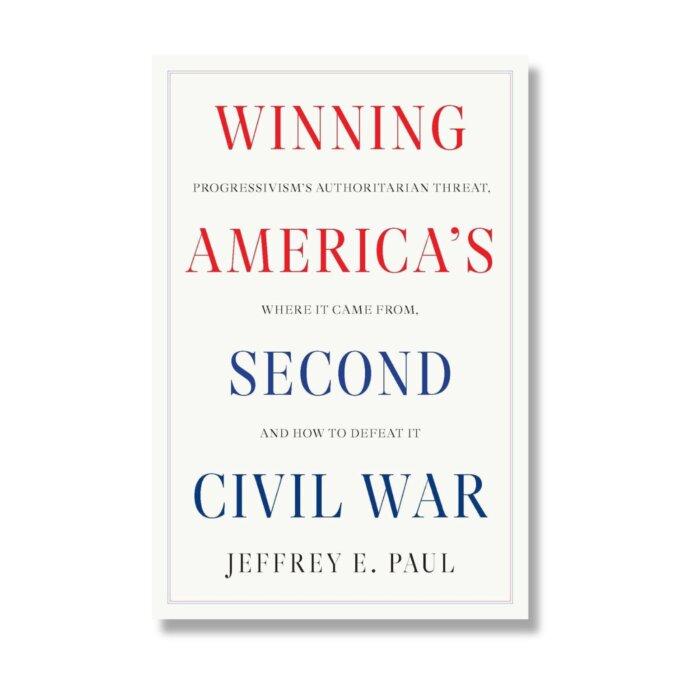
A History Of The American Nation
A patriotic poem by Ted Schneider
Of Cars and Kids
Why should our kids have to settle for a Trabant, or a Pyonghwa, education when they could have a BMW?
A Nation Divided
Poem by an American Patriot
What Is Going on Here?
There are two major things plants need to survive and continue generating our life saving oxygen. The first is CO2, and the second is sunshine.
Inspired Stories
Empower the World with Your Story: Share Love, Inspiration, and Hope with Millions
The ‘Fast and Furious’ Actor Who Left Hollywood for a Traditional Lifestyle
Lucas Black, who stars in the new film ‘Unsung Hero,’ takes his sons fishing and hunting, while instilling in them confidence and a sense of responsibility.
Special Coverage
Special Coverage
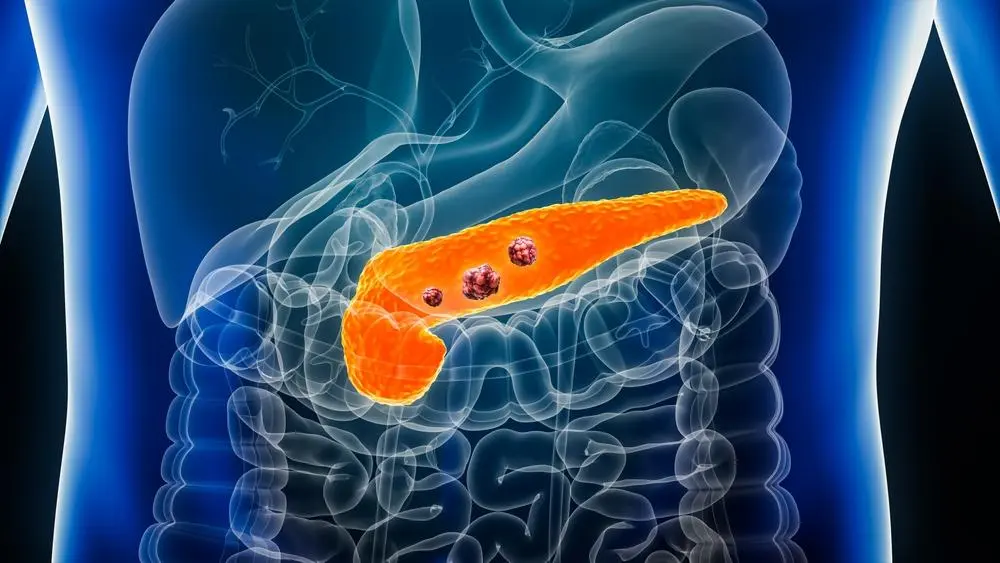
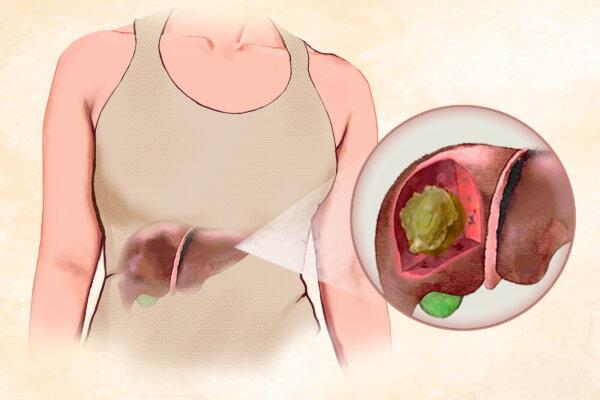
Potential Early Signs of Pancreatic Cancer: Insights From Clinical Cases
Pancreatic cancer can present with symptoms often associated with other illnesses—following the trail of such signs early on could help with early diagnosis.
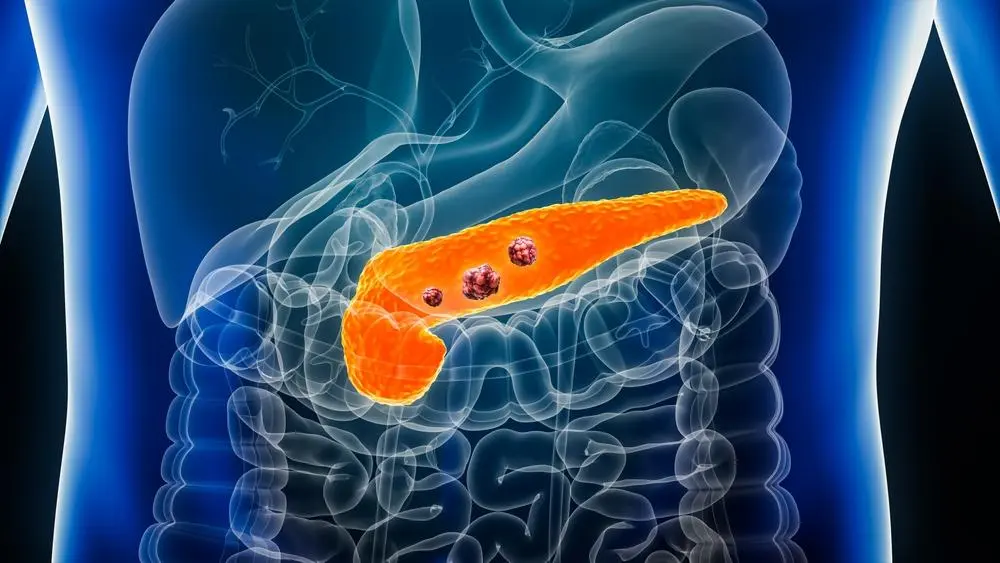
Potential Early Signs of Pancreatic Cancer: Insights From Clinical Cases
Pancreatic cancer can present with symptoms often associated with other illnesses—following the trail of such signs early on could help with early diagnosis.
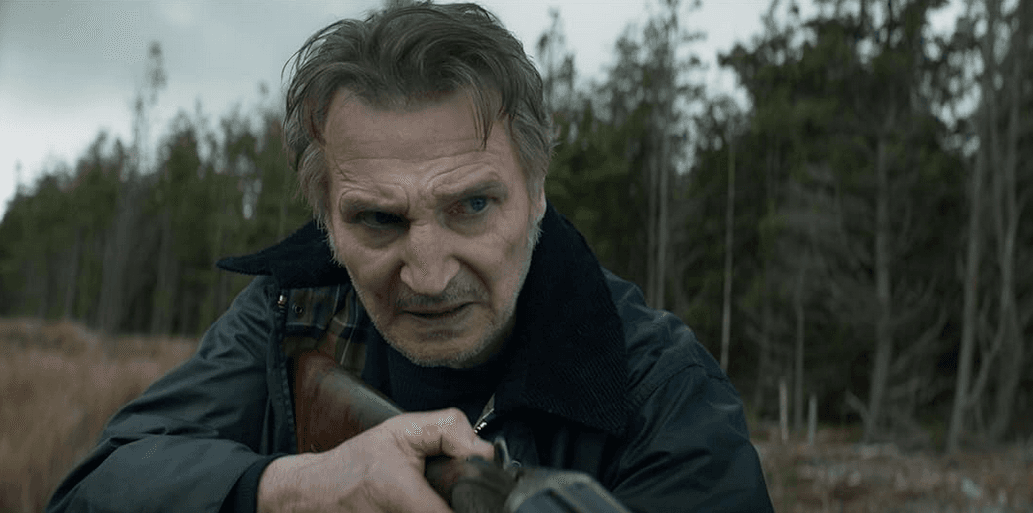
‘In the Land of Saints and Sinners’: A Powerful Irish Tale
Like Brad Pitt’s line in ‘The Devil’s Own’: ‘It’s not an American story—it’s an Irish one,’ ‘Saints and Sinners’ features an all-Irish cast doing IRA things.

‘Nowhere Special’: A Father and Son Tale for the Ages
A dad in his last days searches for the best future for his little boy.
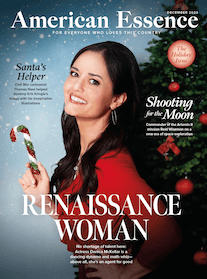
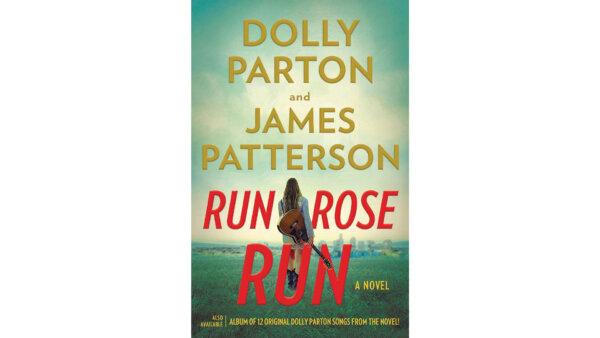
‘Run, Rose, Run’: Run Away With Dolly Parton and James Patterson
Set against Nashville’s vibrant music scene, this collaborative novel is a gripping tale of secrets, ambition, and the pursuit of a dream at all costs.
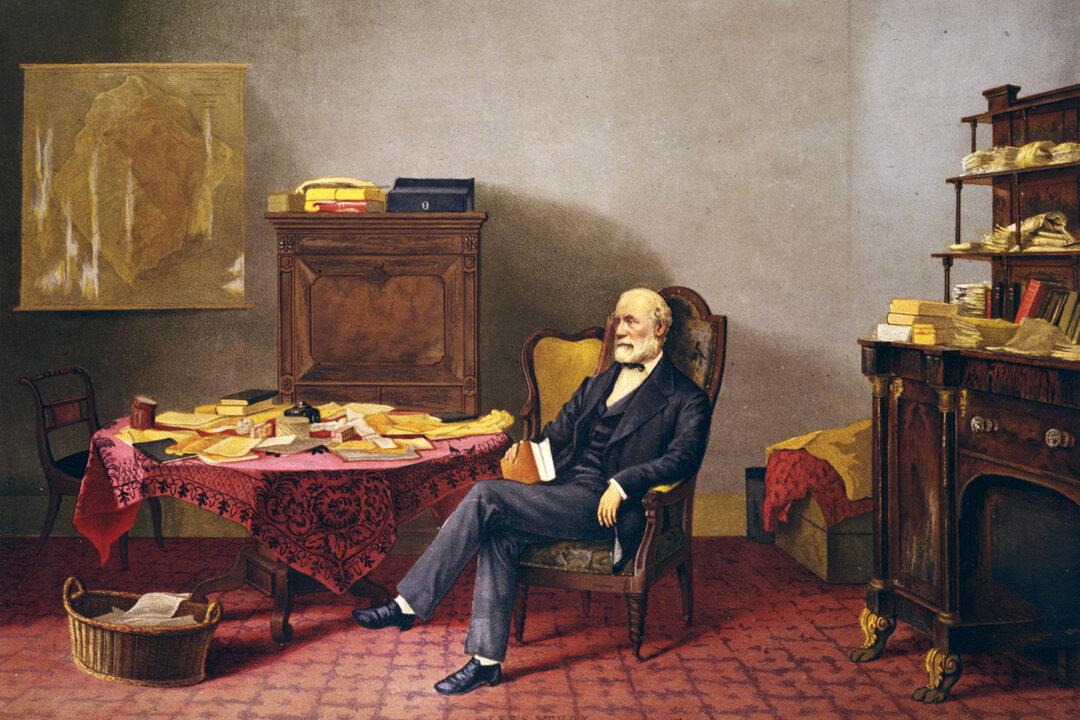
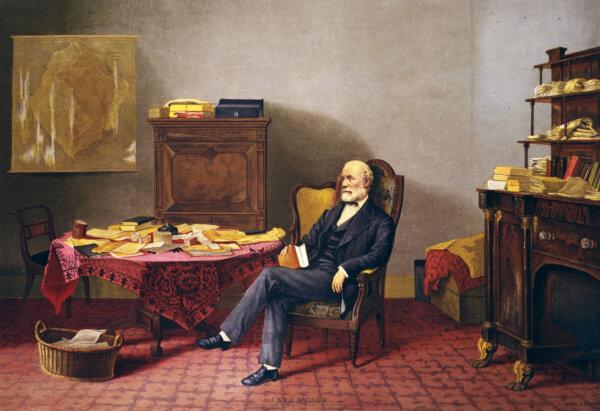
The Two Reputations of Robert E. Lee
While those in the past saw Lee’s stellar qualities, today, some cannot see that he was a man defined, like all of us, by his time.
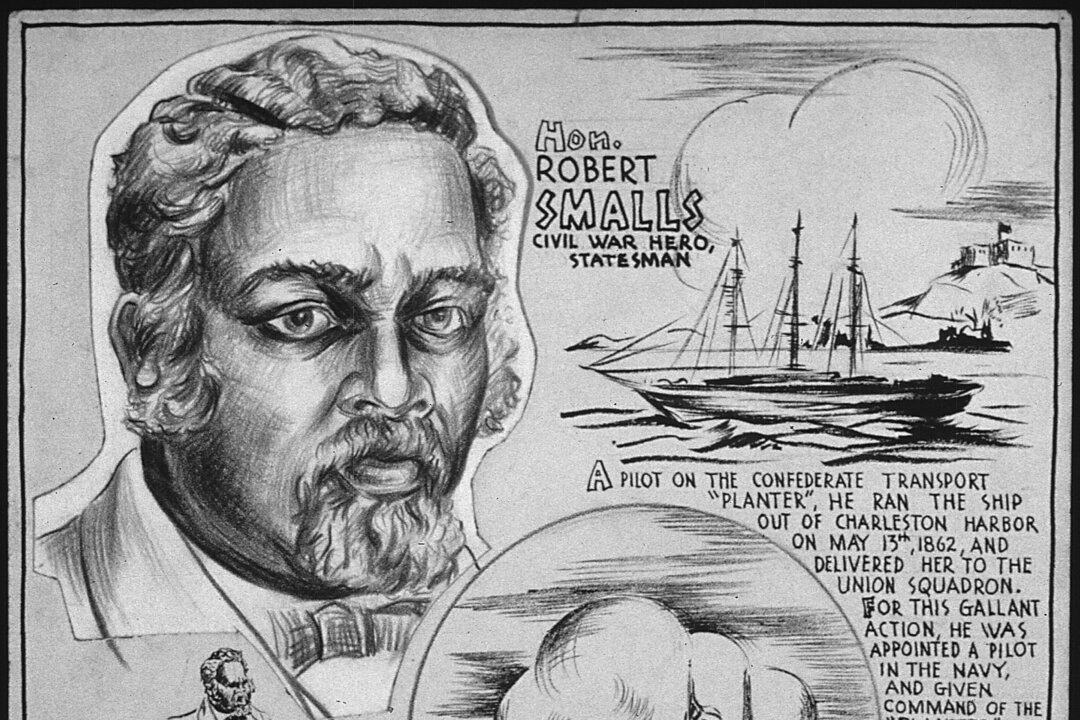
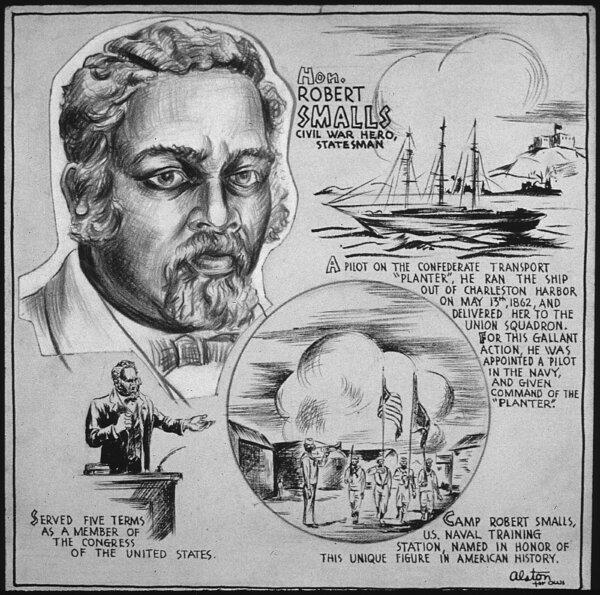
Robert Smalls: Navy Captain and Reconstruction-Era Politician
This former slave would not let anything stop him on the road to freedom.
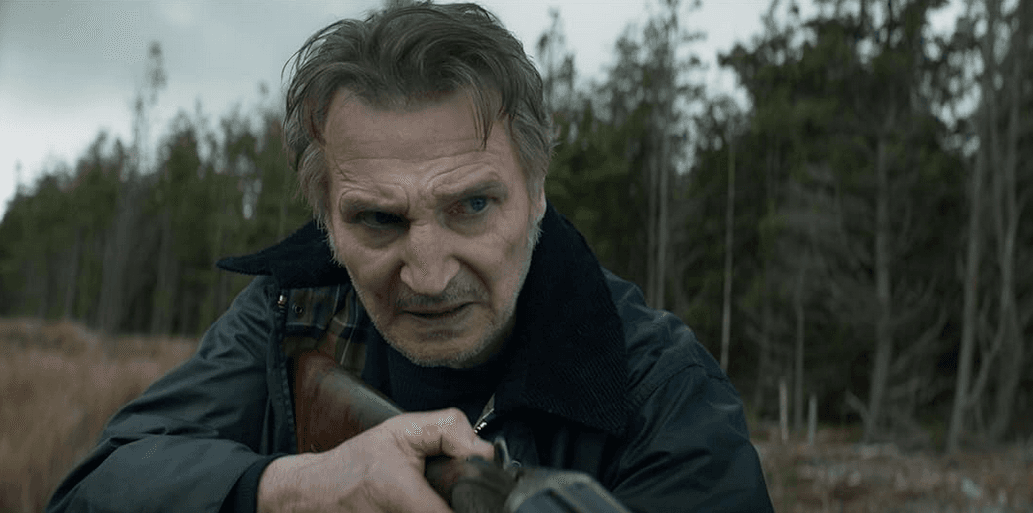
‘In the Land of Saints and Sinners’: A Powerful Irish Tale
Like Brad Pitt’s line in ‘The Devil’s Own’: ‘It’s not an American story—it’s an Irish one,’ ‘Saints and Sinners’ features an all-Irish cast doing IRA things.

What We Can Learn From the Greek Island Where People Live to 100
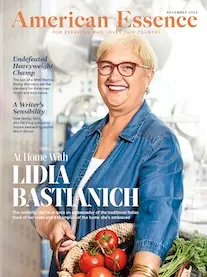
Greek food expert Diane Kochilas, who has run a cooking class from her family home on Ikaria for two decades, shares how to eat and live the Ikarian way.

Michigan Lawmakers Try to Put Brakes on Mackinac Island’s E-bike Riders
Mackinac Island doesn’t have cars but the speed of e-bikes are becoming a problem.

Taking the Kids: To the Smithsonian Museums
The Smithsonian Institution is the world’s largest museum, education and research complex.

Airbnb Rentals Could Be Harder to Come by in Hawaii. Here’s Why and When That Might Happen
New bills will give counties the power to limit short-term rentals amidst housing shortages.
Michigan Lawmakers Try to Put Brakes on Mackinac Island’s E-bike Riders
Mackinac Island doesn’t have cars but the speed of e-bikes are becoming a problem.