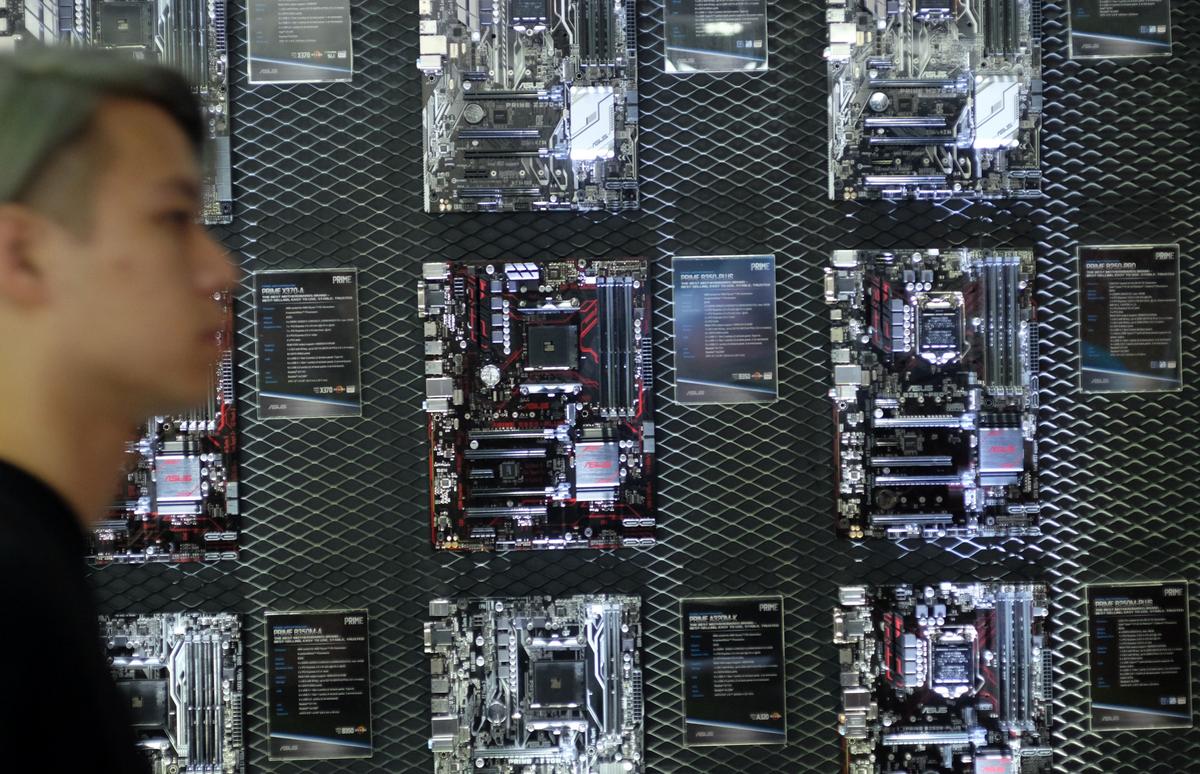
A bombshell report, published by Bloomberg on Oct. 4, claimed that microchips with spyware were being planted into server boards manufactured in China. Those servers were used by major tech firms such as Apple and Amazon, according to the report.
Since the report was published, Taiwanese motherboard manufacturers have gone on alert, accelerating their plans to move production out of China—an undertaking many had already begun since the U.S.-China trade war threatened to impose tariffs on their goods, DigiTimes, a Taiwan-based news website covering the global IT industry, reported on Oct. 8, citing people in the industry that it didn’t identify.The manufacturer of the allegedly manipulated servers, Supermicro, is a U.S.-based company that was founded by a Taiwanese engineer. It makes up more than 11 percent of the global motherboard server market. The company’s motherboards can be found in MRI machines, weapons systems, as well as servers for banks, hedge funds, cloud computing providers, and more.
In fact, many of the world’s major motherboard suppliers—most of them Taiwan-based companies—manufacture their servers in mainland Chinese factories.
While Apple, Amazon, and Supermicro have since denied the claims in the Bloomberg article, the report has exposed the security risks involved with manufacturing in China and vulnerabilities in the tech supply chain.
Moving Out of China
Inventec, a Taiwanese motherboard maker that supplies to computer brands such as Dell and HP, kicked off an expansion of its plant located in northern Taiwan back in September, according to the report. U.S. exports account for 20 to 25 percent of Inventec’s motherboard shipments.
Wistron, another Taiwanese manufacturer, was considering moving motherboard production to the Philippines, according to Japanese business publication Nikkei Asian Review.
Meanwhile, Quanta Computer has already begun increasing production in U.S. and German facilities, and Foxconn, Compal, and Pegatron are among other Taiwan-based manufacturers with plans to relocate production out of China.
Of the top 20 major corporations that export to the United States, 15 are corporations with capital from Taiwan, most of them science and tech firms, according to the Hong Kong Economic Times.
And of the top 100 Chinese joint-venture corporations that exported to the United States last year, 40 percent were joint ventures with Taiwanese firms, which is a major reason why the Taiwan IT sector worries about the U.S.-China trade war.