NEW YORK—Kevin Tillman doesn’t consider himself a hero. But to many young girls and boys, he is their champion, an unsung hero in a dark world. His work takes pedophiles and child pornographers off the streets. And he helps save kids from nightmare scenarios.
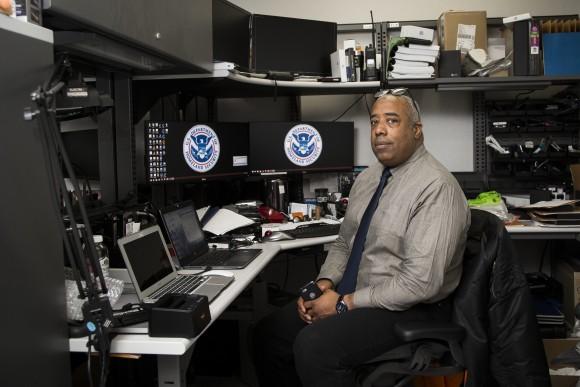
Tillman is a computer forensics expert working for ICE (Immigrations and Custom Enforcement) Homeland Security Investigations (HSI) in New York. He is a 29-year military veteran who retrained as a Human Exploitation and Rescue Operative (HERO) after retiring in 2015. The HERO program gives veterans, especially those who are wounded, a chance to retrain and fight crime in a different way.
Tillman is the first HERO in the New York HSI office, and he brings his special operations experience to his new role.
“It was very humbling to get involved in this and see that there’s this hidden society of people that’s so massive. I was unaware that pedophilia was such a large society,” Tillman said on April 28.
“I mean, who can question [cracking down on] child pornography or human trafficking—those are things most people want to see diminished, or at least depleted.”
A recent successful case involved an individual who visited a website that was being monitored. During a subsequent search at his home, child pornography was found on one of his computer systems. Tillman’s job was to meticulously sort through all of the evidence on the hard drive.
He discovered compromising photos between a young girl and her grandfather, who lived at the home with the father.
“The granddaughter was removed from the home,” Tillman said. “And it appears that the father didn’t know that the grandfather was involved with the child.”