SPECIAL COVERAGE
Read More
Read More
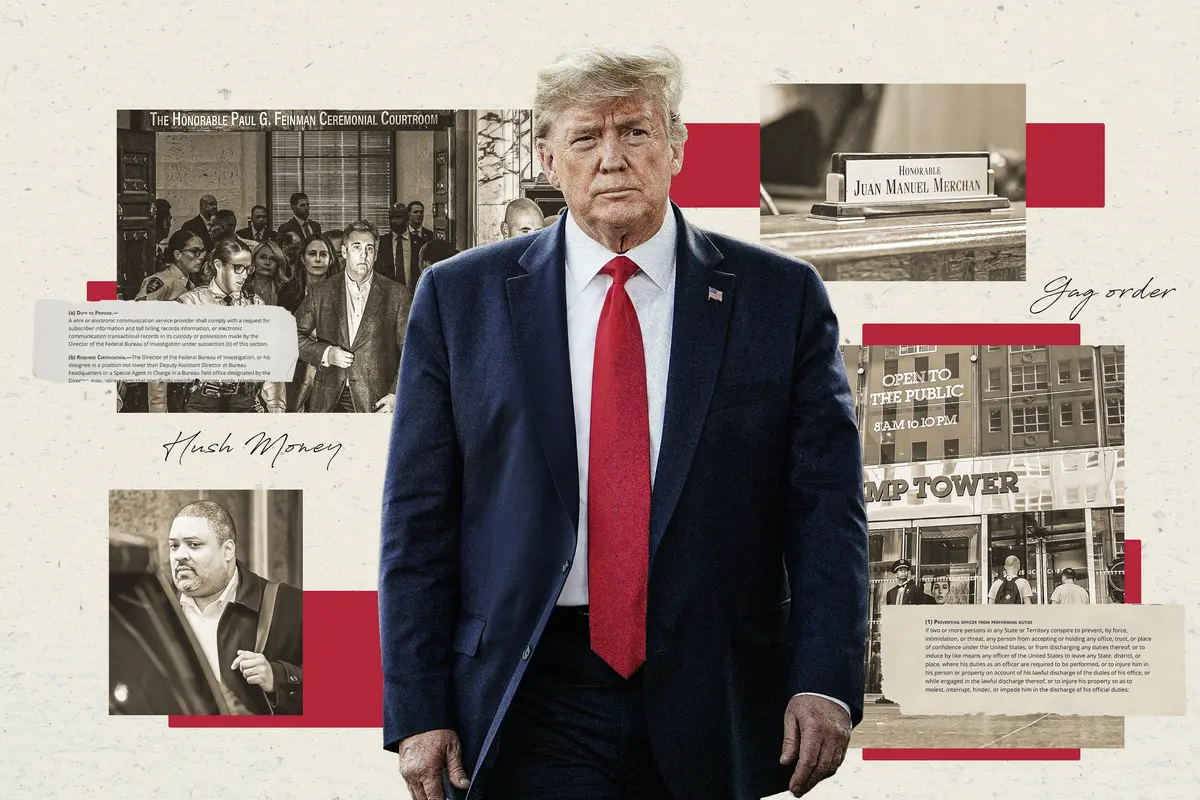
Jury Selection Nearing End on Third Day for Trump Criminal Trial
One juror had changed her mind and the other was dismissed after concerns raised over the credibility of his answers.
Jury Selection Nearing End on Third Day for Trump Criminal Trial
One juror had changed her mind and the other was dismissed after concerns raised over the credibility of his answers.
Trending Videos
Top Premium Reads
Top Stories
Most Read
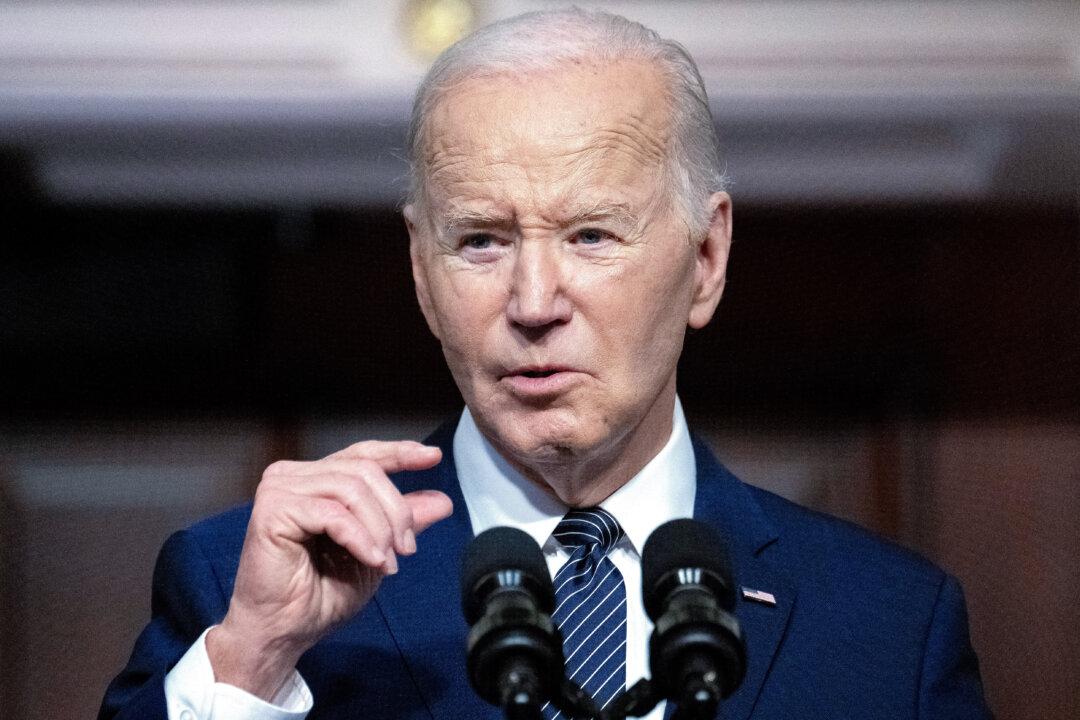
Biden Admin Announces New Sanctions Targeting Iran’s Drone Industry After Attack on Israel
“Today, we are holding Iran accountable—imposing new sanctions and export controls on Iran.”
Senate Overcomes Procedural Hurdle to Reauthorize Spying Authority
The bill now set for swift passage in the Senate does not require intelligence officials have a warrant to search Americans’ data and communications.
Senate Commerce Chair Endorses Bill That Could Expel TikTok From US
The legislation prohibits entities deemed sufficiently owned or controlled by individuals within an adversary country from operating within the United States.
Science Magazine Publisher Apologizes for Dismissing Theory That COVID-19 Came From Lab
‘That was flippant, and I shouldn’t have done that,’ Holden Thorp said.
D-Mannose for UTIs: Miracle Supplement or Just Hype?
Nature’s UTI defender faces new scrutiny. Can it stand the test of science?
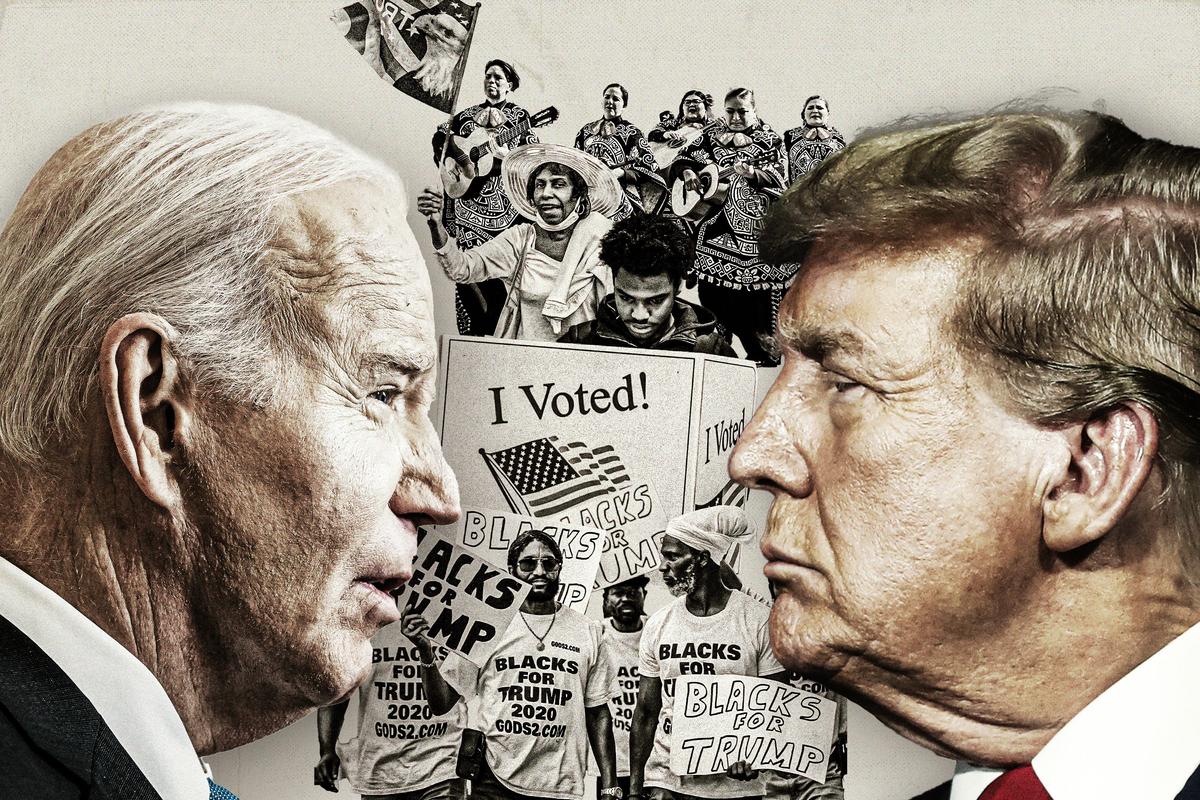
What the Polls Aren’t Telling Us About Trump’s Lead
Hidden voters, third-party candidates, and turnout figures compound uncertainty over the outcome.
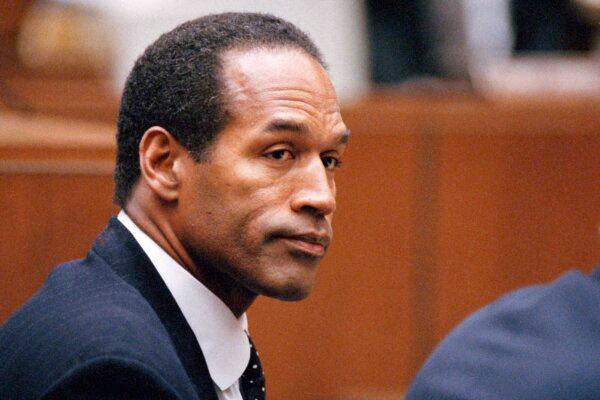
Juror in ‘Hush-Money’ Trial Dismissed Citing Concerns Over Being Impartial, Identity Being Made Public
The juror said her family and friends had questioned her about whether or not she was a juror based on media reports.
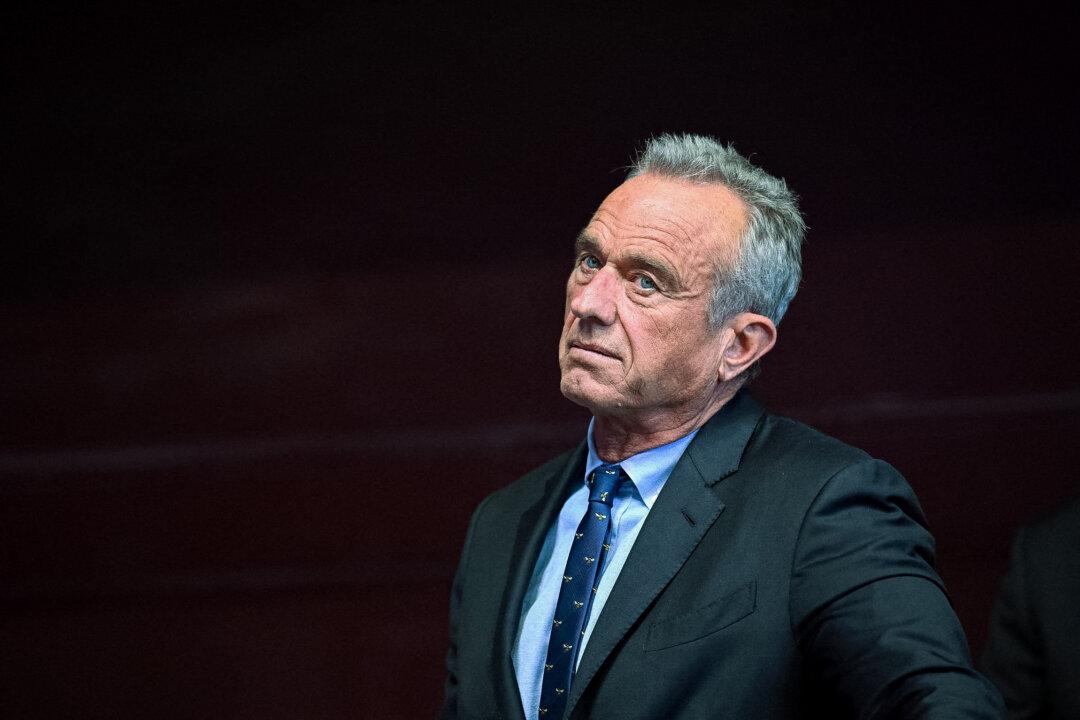
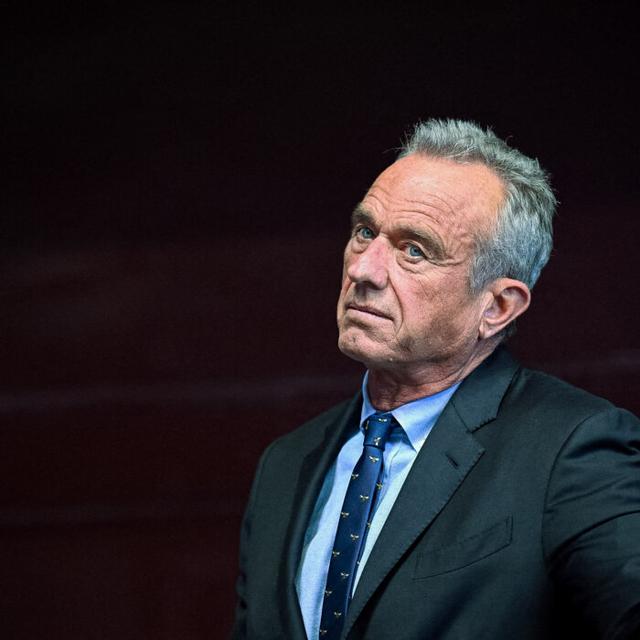
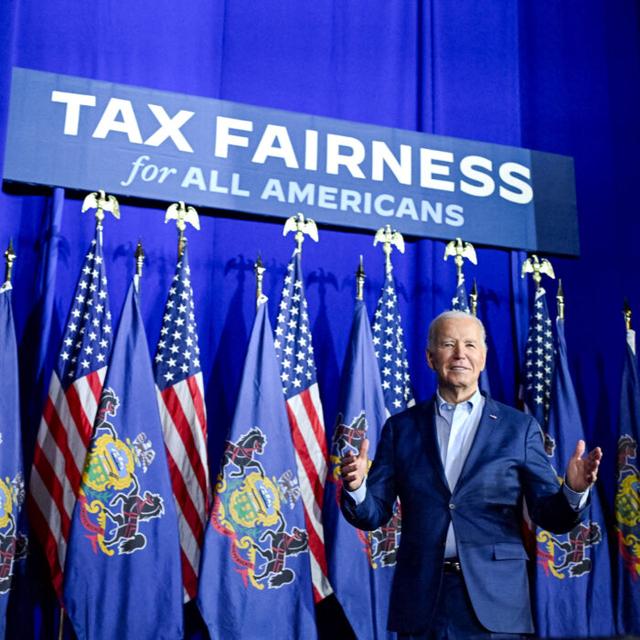
Biden Wins Endorsement of Kennedy Family Members
More than 15 members of the Kennedy family endorsed the president at a campaign event in Philadelphia.
Supreme Court Considers If Death Row Inmate Deserves New Sentencing
An Arizona prisoner argues his lawyer didn’t do enough to find mitigating evidence.
Top Military Official Lied About Jan. 6: Whistleblowers
Army Secretary Ryan McCarthy was among senior officials who did not tell the truth about what happened on Jan. 6, 2021, National Guard officials say.
Trump Lawyers Say Key Witness Refused Subpoena as Day 3 of ‘Hush-Money’ Trial Starts
President Trump made no comments to the media.
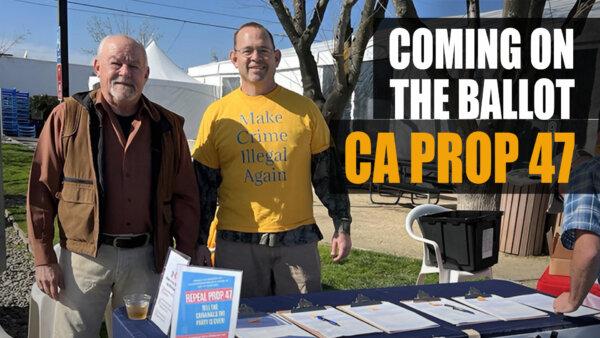
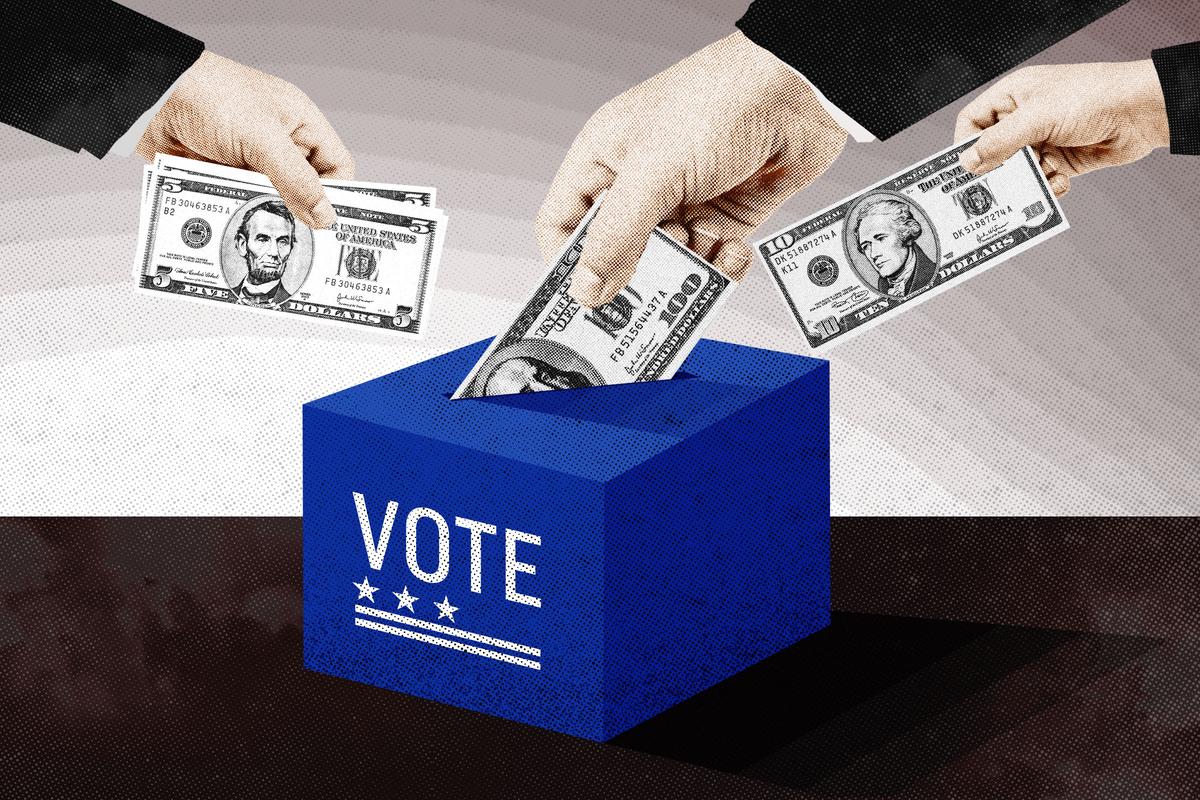
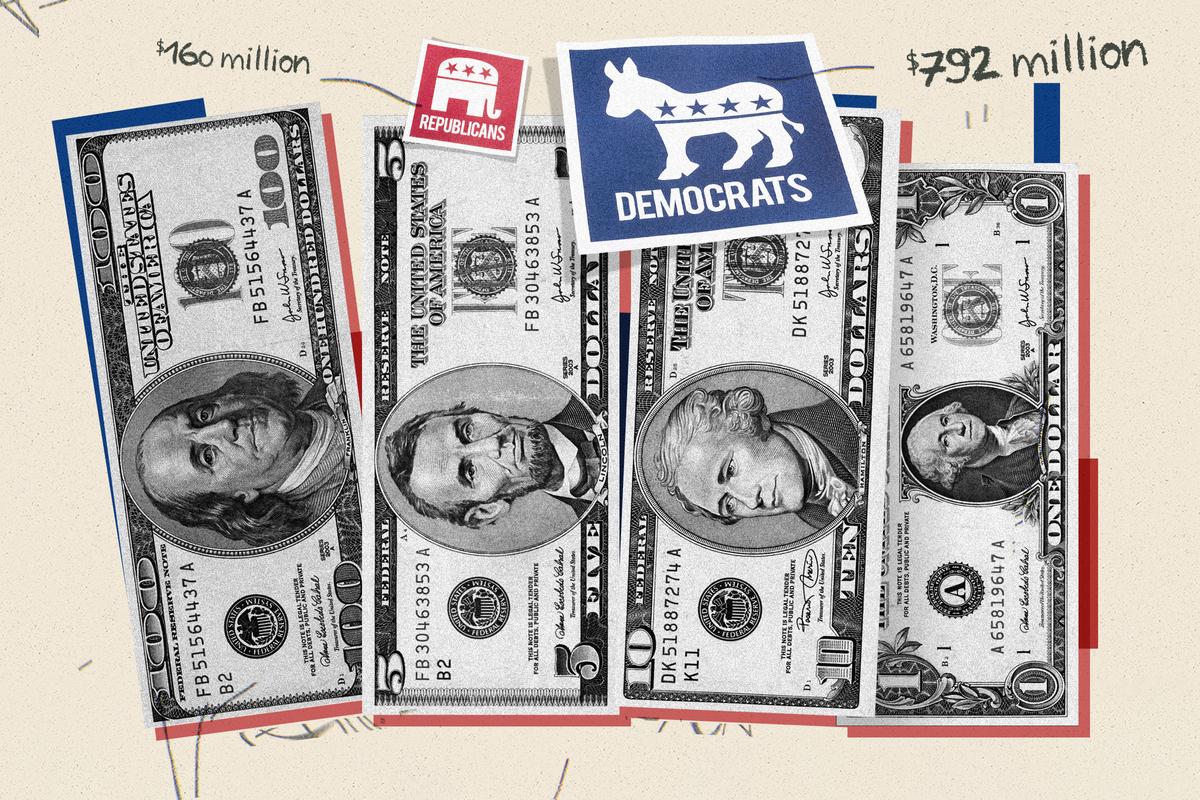
How Social Media Censorship May Impact the 2024 Presidential Election
Big Tech appears to be dusting off the same censorship tactics it used to influence the outcome of the 2020 presidential election cycle, an expert said.
Few Side Effects Conclusively Linked to COVID-19 Vaccines: National Academies
Organization claims just a handful of side effects definitely or likely are caused by the vaccines.

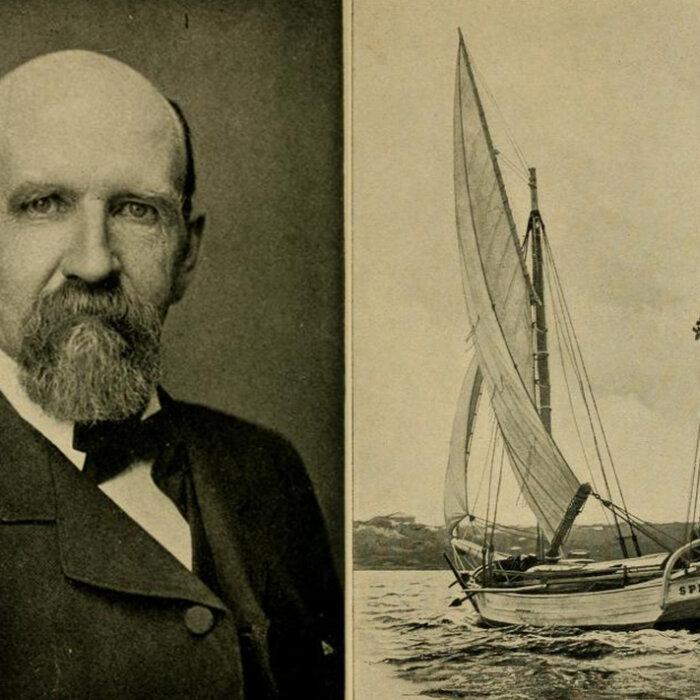
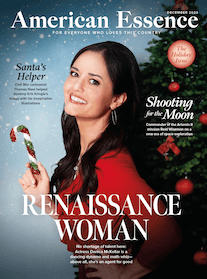
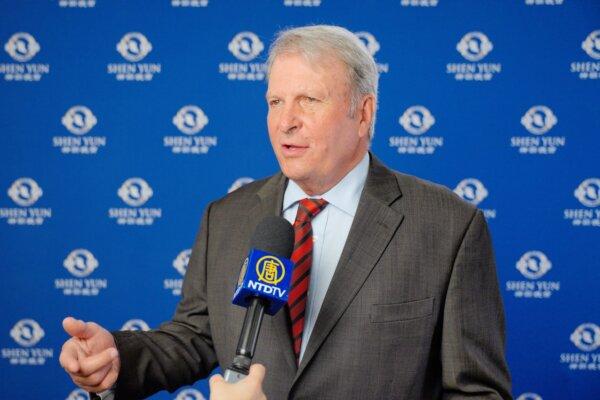
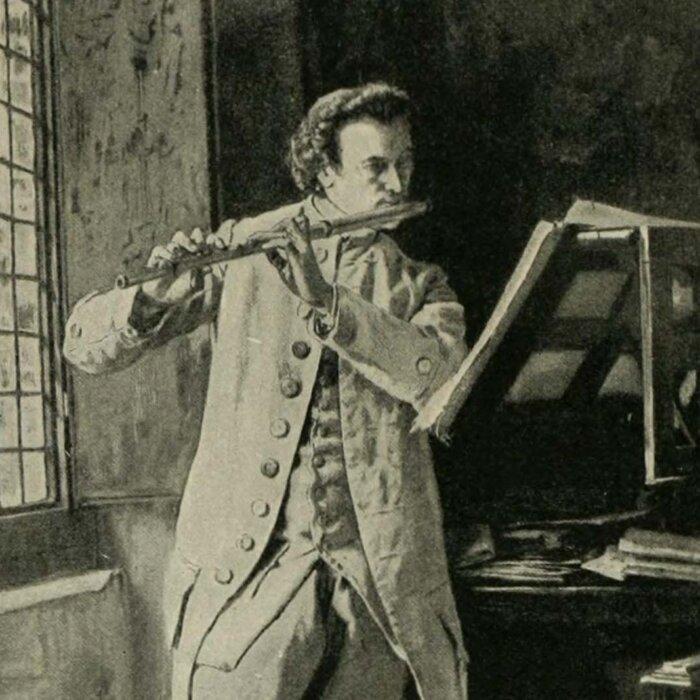
The American Mozart: Composer Timothy Olmsted
Timothy Olmsted’s lifelong dedication to music made him one of the country’s earliest influential musicians.
The American Mozart: Composer Timothy Olmsted
Timothy Olmsted’s lifelong dedication to music made him one of the country’s earliest influential musicians.
Epoch Readers’ Stories
Wisdom From a Retired Cowboy Artist
I have lived the life of the sculptures I have made.
Section 3 of 14th Amendment Not Applicable for Ruling Trump out of 2024
I don’t believe that Section 3 of 14th Amendment is self-executive and therefore can not be applied directly by the court.
Inspired Stories
Empower the World with Your Story: Share Love, Inspiration, and Hope with Millions
Special Coverage
Special Coverage
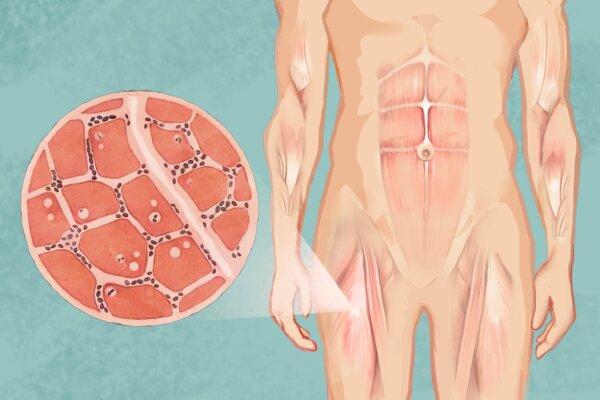
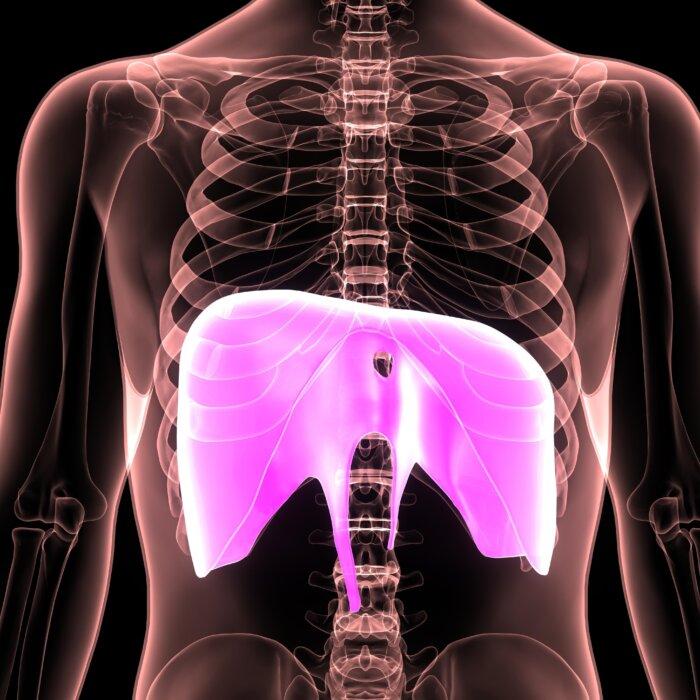
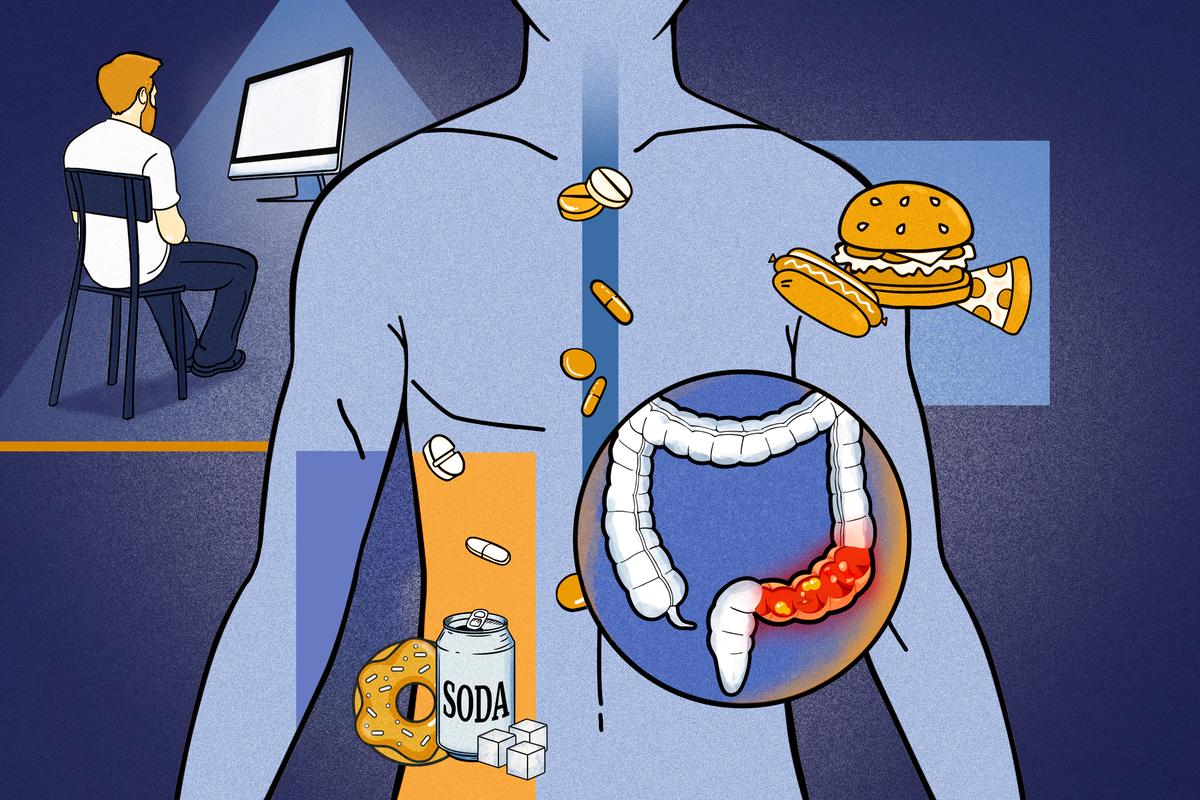
Improve Leaky Gut Syndrome With These Ancient Approaches
Leaky gut can lead to fatigue and gastrointestinal discomfort. Learn how traditional Chinese medicine approaches the issue.
Improve Leaky Gut Syndrome With These Ancient Approaches
Leaky gut can lead to fatigue and gastrointestinal discomfort. Learn how traditional Chinese medicine approaches the issue.

‘Hart’s War’: Soldiers Shaping War and Being Shaped by It
A court-martial at the POW camp is not what it seems to be in this film by director Gregory Hoblit.

‘Monsieur Chopin: A Play With Music’
This one-man play celebrates the life and music of one great composer.

‘Tim’s Vermeer’: Duplicating a Masterwork
Magicians Penn Jillette and Teller lend their talents to a documentary that reveals a few centuries-old secrets.

S. Truett Cathy: Founder of Chick-fil-A
This entrepreneur called on his ethic of hard work to build a successful fast food franchise.

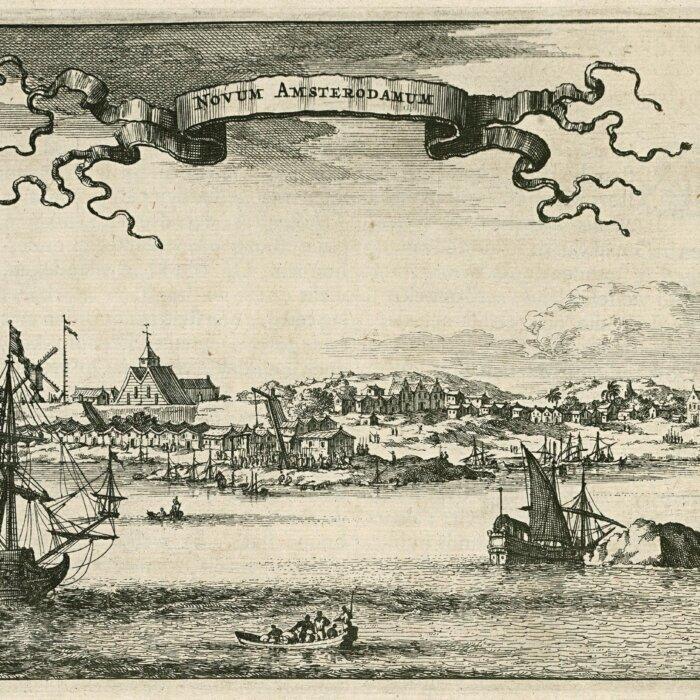
Rembrandt’s Sole Seascape and the Great Heist
Stolen from the Isabella Stewart Gardner Museum in 1990, ‘Christ in the Storm on the Sea of Galilee’ along with two other Rembrandts are still missing.

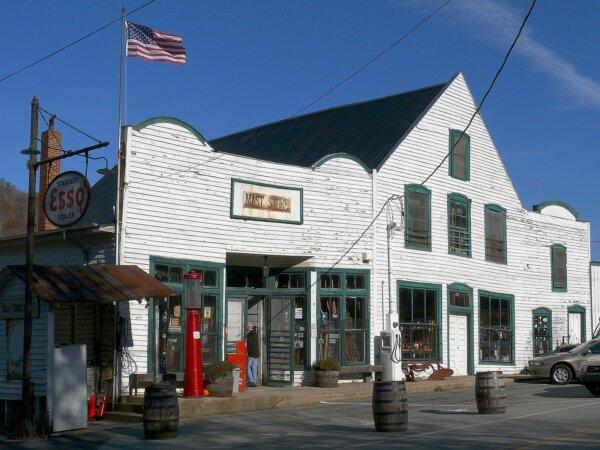
Where Time Stands Still: Mast General Store
The general stores encapsulates a bygone era for travelers in North Carolina.

‘Hart’s War’: Soldiers Shaping War and Being Shaped by It
A court-martial at the POW camp is not what it seems to be in this film by director Gregory Hoblit.

The ‘French 75’ Cocktail Will Make You Feel Like You’re at a Fancy Restaurant
A French 75 is a great classic cocktail to celebrate milestones or special events with.

The Next Total Solar Eclipse Will Hit These 2 Popular World Travel Destinations in 2026
The next total eclipse will fall over Iceland and Spain.

Ed Perkins on Travel: Travel Scams—Anything New?
Hotels are not the only places that have hidden fees.

Helsinki and Tallinn: Pearls of the Baltic
Finland and Estonia—are not only neighbors, but soul sisters.
The Next Total Solar Eclipse Will Hit These 2 Popular World Travel Destinations in 2026
The next total eclipse will fall over Iceland and Spain.
















![[LIVE on 4.19 1PM ET] How Diet, Lifestyle Could End 80 Percent of Diabetes, Cancer, Other Disease](/_next/image?url=https%3A%2F%2Fimg.theepochtimes.com%2Fassets%2Fuploads%2F2024%2F04%2F13%2Fid5628731-Food-Matters-web-1920x1080-1.jpeg&w=1200&q=75)

![[LIVE on 4.19 1PM ET] How Diet, Lifestyle Could End 80 Percent of Diabetes, Cancer, Other Disease](/_next/image?url=https%3A%2F%2Fimg.theepochtimes.com%2Fassets%2Fuploads%2F2024%2F04%2F13%2Fid5628731-Food-Matters-web-1920x1080-1-1080x720.jpeg&w=1200&q=75)
























































































![[PREMIERING 4/18, 9PM ET] Peter Schweizer: Inside the CCP’s Fentanyl Warfare Strategy to Kill Americans](/_next/image?url=https%3A%2F%2Fimg.theepochtimes.com%2Fassets%2Fuploads%2F2024%2F04%2F18%2Fid5632293-240417-ATL_Peter-Schweizer_HD_TN-600x338.jpeg&w=1200&q=75)