SPECIAL COVERAGE
Read More
Read More
US Economic Growth Slows to 1.6 Percent in 1st Quarter, Lowest Since 2022
Consumer and government spending slows.
US Economic Growth Slows to 1.6 Percent in 1st Quarter, Lowest Since 2022
Consumer and government spending slows.
Top Premium Reads
Top Stories
Most Read
Supreme Court to Hear Trump’s Presidential Immunity Appeal
The high court will weigh whether Trump is immune from prosecution in the federal election case in a decision that could delay his trials further into the year.
A Peaceful Appeal for Freedom 25 Years Ago Still Echoes Today
About 10,000 people quietly congregated in Beijing on a spring day in 1999, now remembered as the April 25 appeal—the largest protest in China’s recent history.
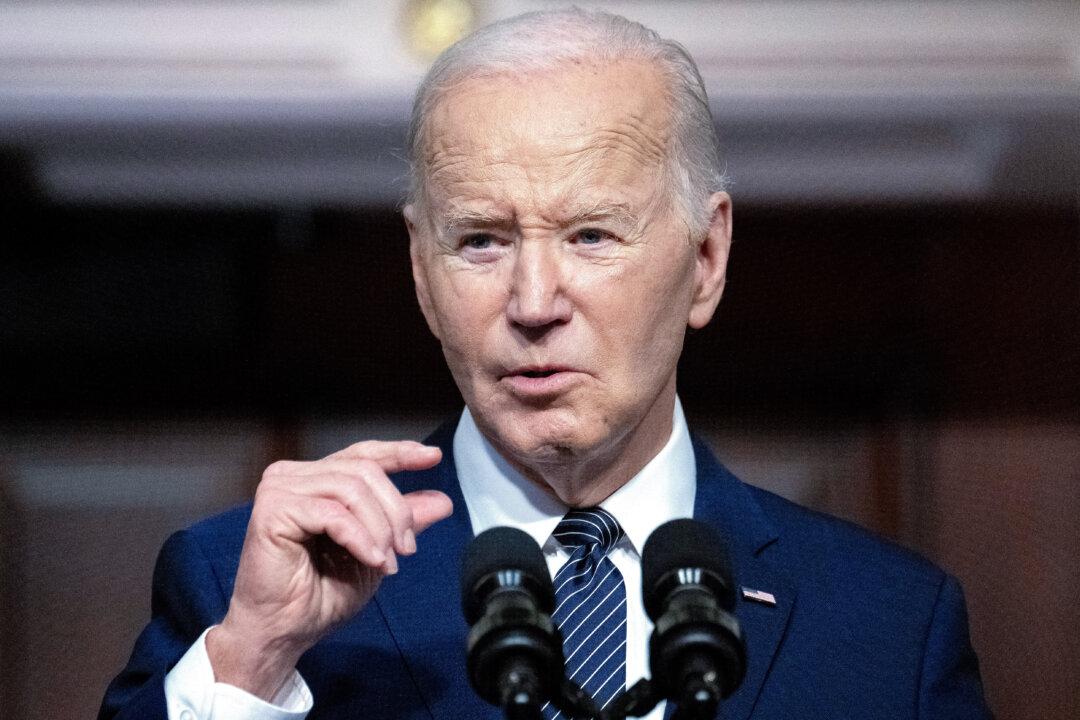
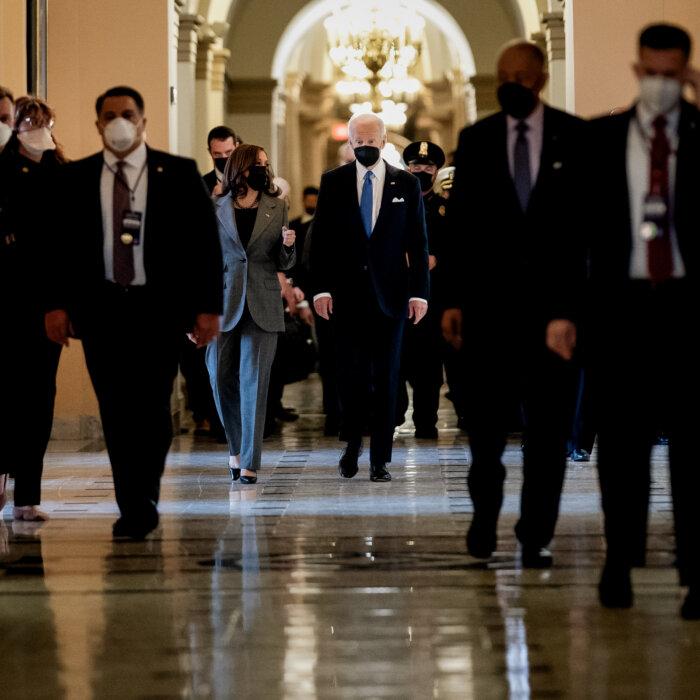
Biden to Visit Syracuse to Tout New Investment in Chip Manufacturing
Micron will receive over $6 billion in government grants to boost domestic production.
Harvard Students Prop Up Tents to Protest Israel-Hamas War
Prime Minister of Israel Benjamin Netanyahu has called the ongoing pro-Palestinian protests across U.S. campuses ‘horrific.’
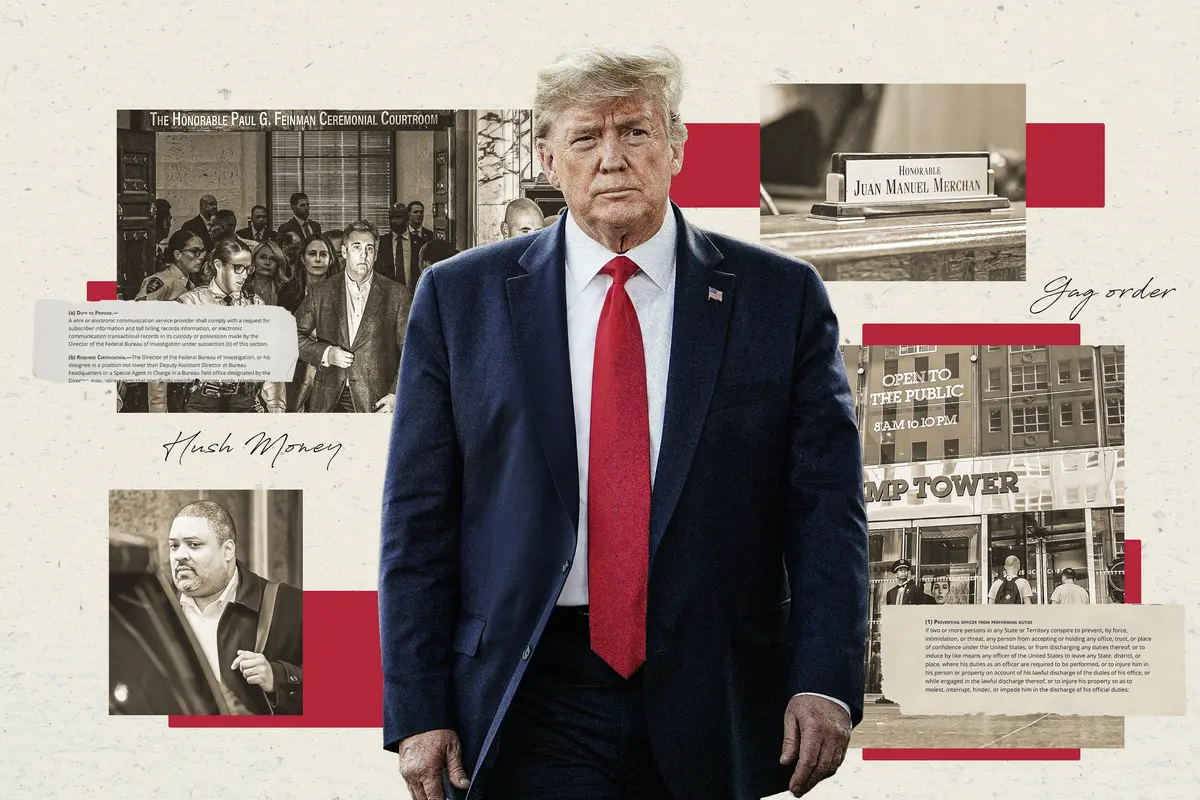
Trump Criticizes New York Judge After His Request to Attend Supreme Court Presidential Immunity Hearing Denied
A ruling on presidential immunity by the Supreme Court is expected by late June. However, initial oral arguments begin on Thursday.
Shareholders, State Officials Allege Political, Religious Discrimination by Bank of America
‘This isn’t the right way to do business in America,’ Indiana State Treasurer Daniel Elliott stated.
Fauci to Testify in Public Hearing on COVID-19 Response, Origins
Dr. Fauci already testified in a closed door hearing and admitted there were serious systemic failures in the public health system during the COVID crisis.
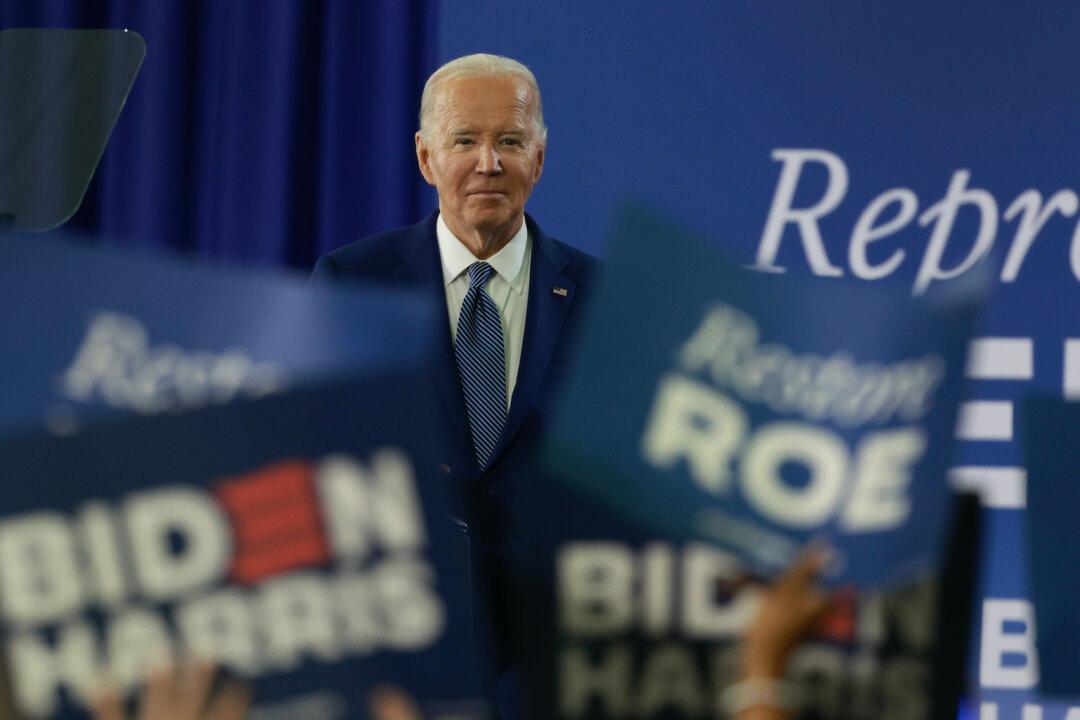
Ohio Republicans and Democrats Negotiate to Ensure Biden’s Ballot Spot
President Biden is expected to be nominated at the Democrat Party’s convention Aug. 19-22 after Ohio’s Aug. 7 certification deadline.
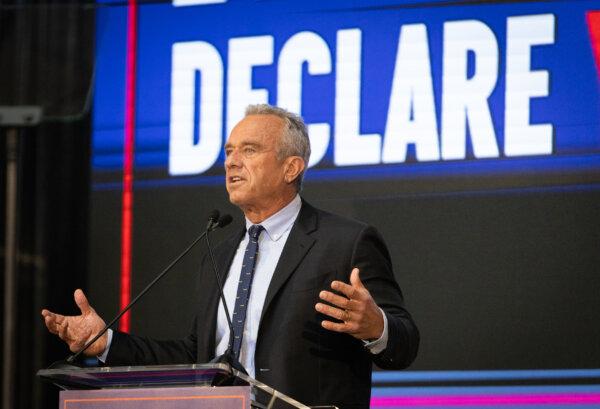
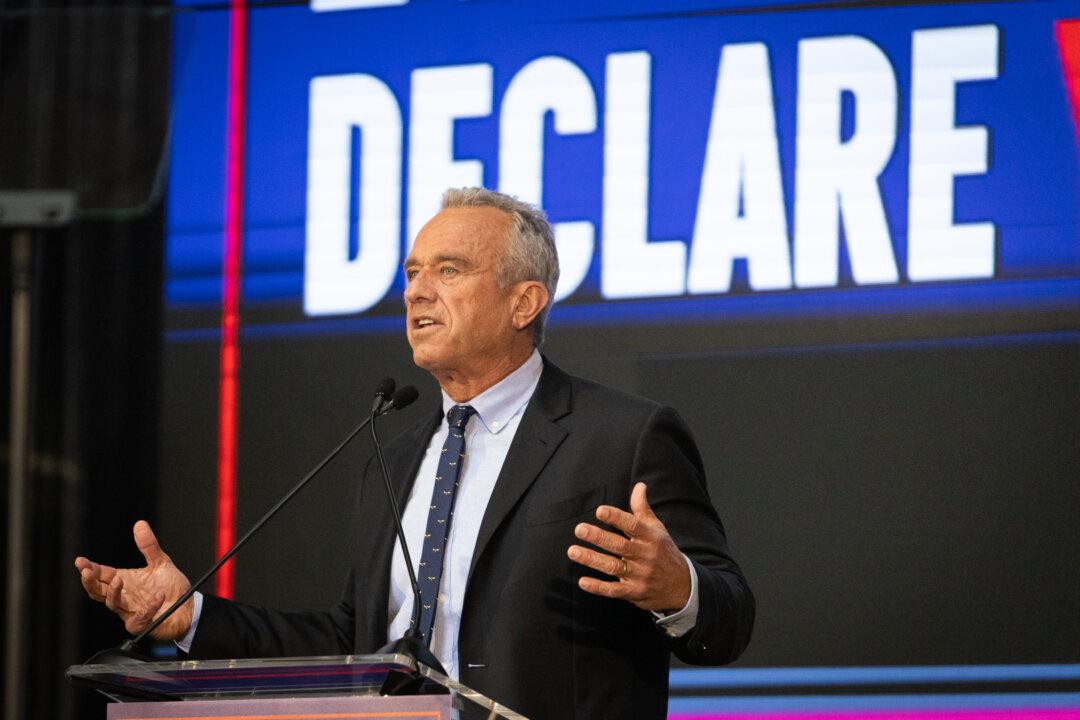
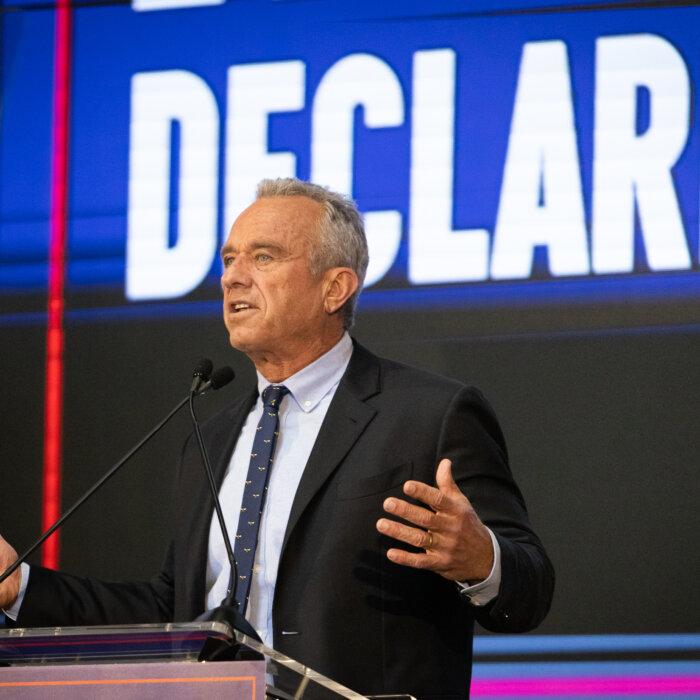
RFK Jr.’s ‘Night of Laughter’ Illustrates Unconventional Fundraising Strategy
To compete with the deep pockets of the Biden and Trump campaigns, Mr. Kennedy employs non-traditional methods to generate money and awareness.
Columbia University Students React to House Speaker Mike Johnson’s Campus Visit
Mr. Johnson called for the resignation of Columbia University President Minouche Shafik.
Editors' Picks
Judge Unseals Documents Showing FBI Discussed ‘Loose Surveillance’ of Trump’s Plane
A large tranche of documents were unsealed by Judge Aileen Cannon on Monday, revealing the FBI’s code name for the probe.
West Virginia Takes Transgender Sports Ban Fight to Supreme Court
‘We’re working to defend the integrity of women’s sports. We must protect our young women,’ said West Virginia Attorney General Patrick Morrisey.
Pentagon Watchdog Opens Probe of DOD Funds to China for Pathogen Research
Outraged lawmakers are demanding answers about American tax dollars going to firms controlled by the Chinese Communist Party.
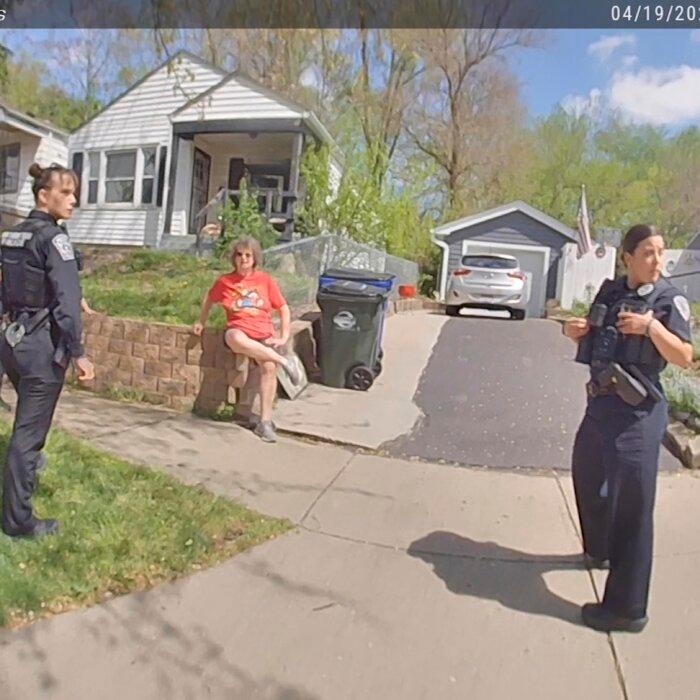
Police Arrest Anti-Israel Protesters on University of Texas Austin Campus
Hundreds of students walked out of class to protest in support of Palestinians, demanding the university divest from Israel.

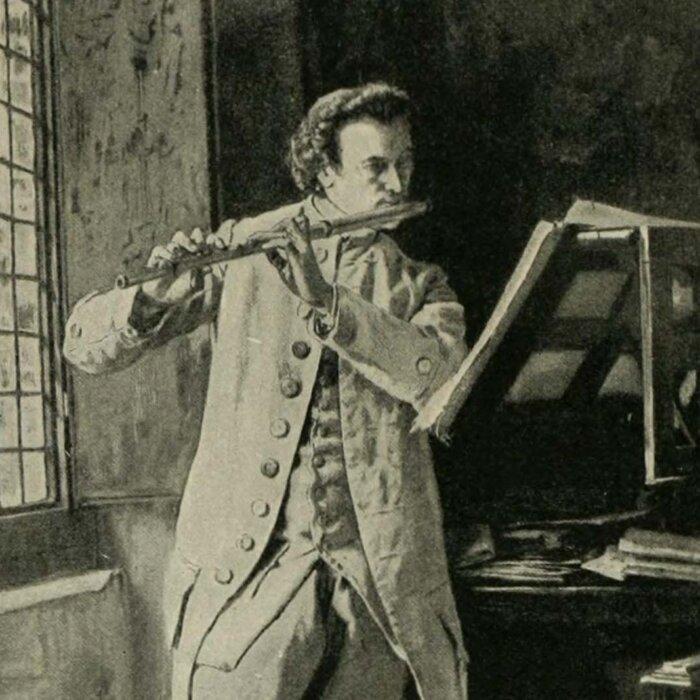
Mahler’s ‘Resurrection’ Symphony: Answering Nihilism
Mahler’s “Resurrection” Symphony is the musical equivalent of “Hamlet.” What led to its creation?
Mahler’s ‘Resurrection’ Symphony: Answering Nihilism
Mahler’s “Resurrection” Symphony is the musical equivalent of “Hamlet.” What led to its creation?
Epoch Readers’ Stories
A Nation Divided
Poem by an American Patriot
What Is Going on Here?
There are two major things plants need to survive and continue generating our life saving oxygen. The first is CO2, and the second is sunshine.
Wisdom From a Retired Cowboy Artist
I have lived the life of the sculptures I have made.
Inspired Stories
Empower the World with Your Story: Share Love, Inspiration, and Hope with Millions
Special Coverage
Special Coverage

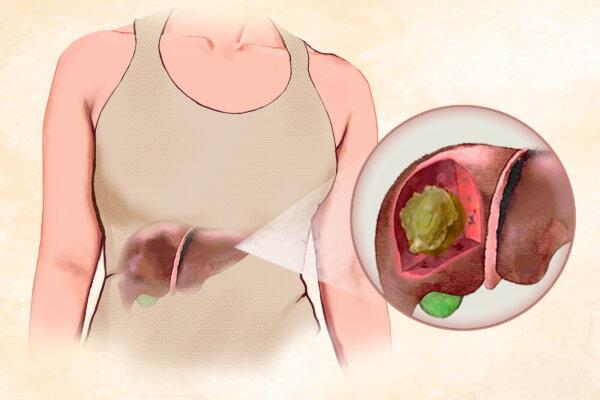
Suffering Symptoms Caused By Prolonged Sitting? Try These 5 Exercises for Relief
Offsetting sitting with exercises throughout the day may alleviate and prevent pain and other consequences of prolonged sitting.

Suffering Symptoms Caused By Prolonged Sitting? Try These 5 Exercises for Relief
Offsetting sitting with exercises throughout the day may alleviate and prevent pain and other consequences of prolonged sitting.

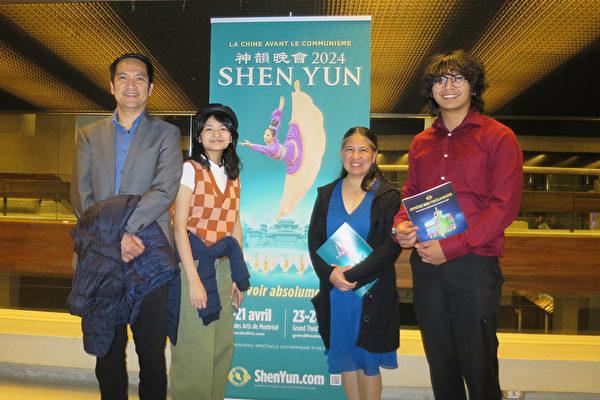
Morality and Opera: A Traditional Message of Good Versus Evil
In this first installment of ‘A Modern Look at Opera,’ we are introduced to the strong moral messages in this classical performing art.

‘Terrestrial Verses’: Censorship Up Close and Personal
Iranians face absurd suppression of their rights by bureaucrats.

Palazzo del Te: A Palace Near Mantua, Italy
In this installment of ‘Larger Than Life: Architecture Through the Ages,’ we visit a duke’s ‘pleasure palace.’
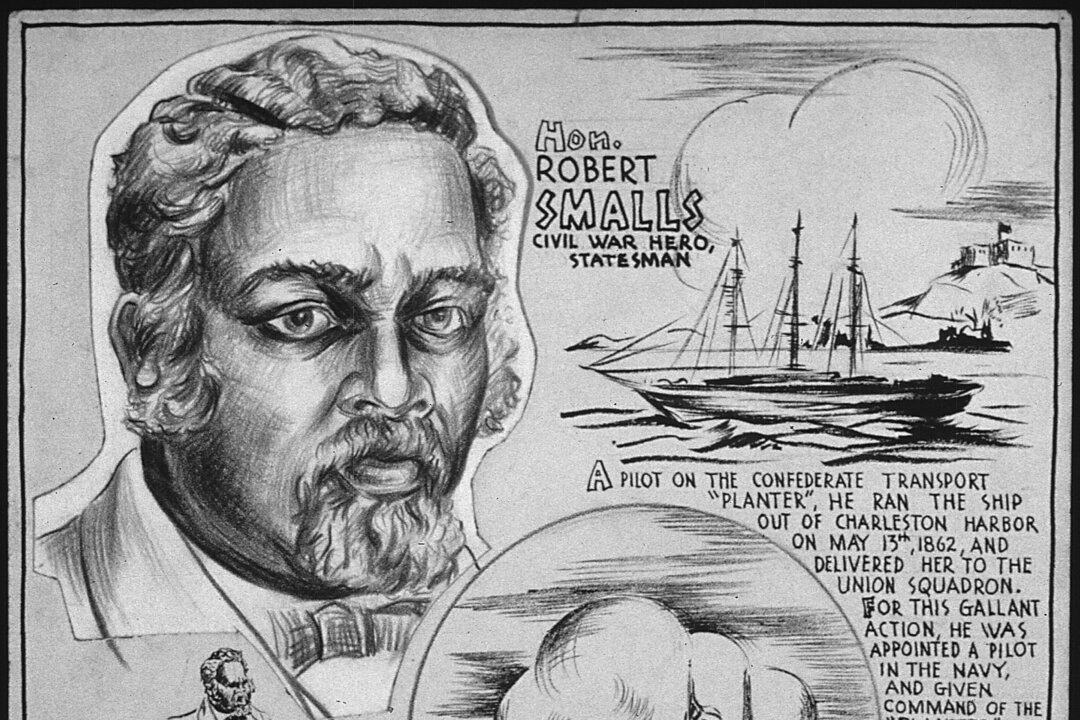
Robert Smalls: Navy Captain and Reconstruction-Era Politician
This former slave would not let anything stop him on the road to freedom.
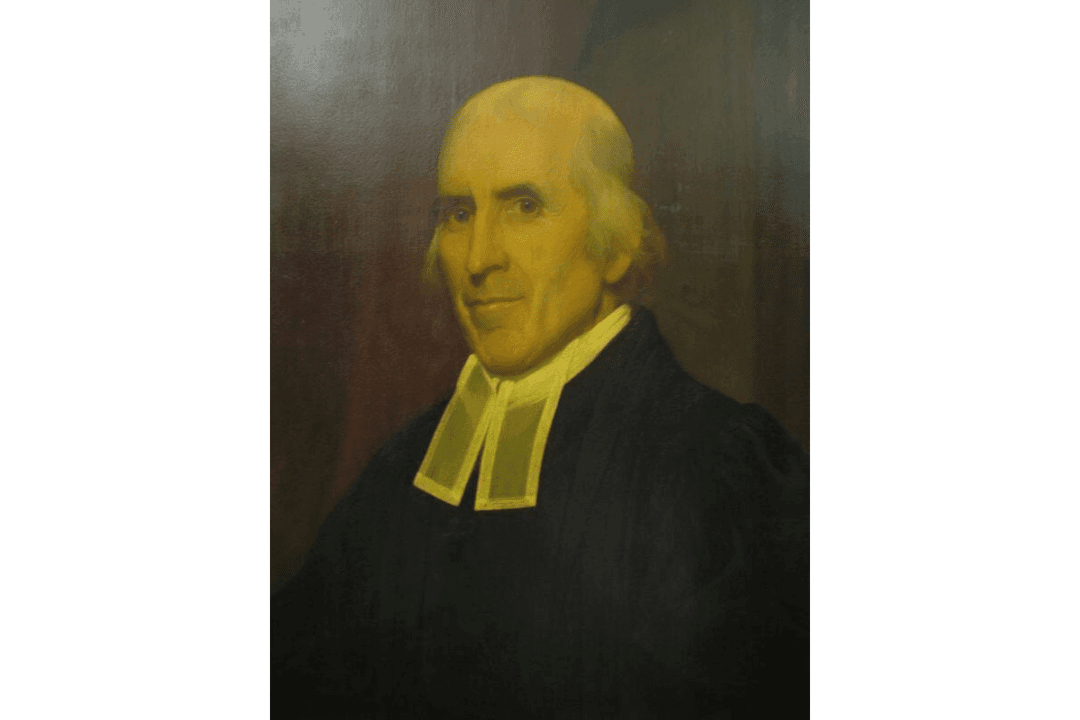
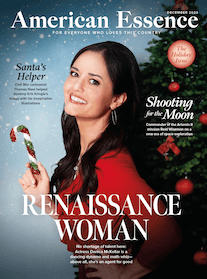
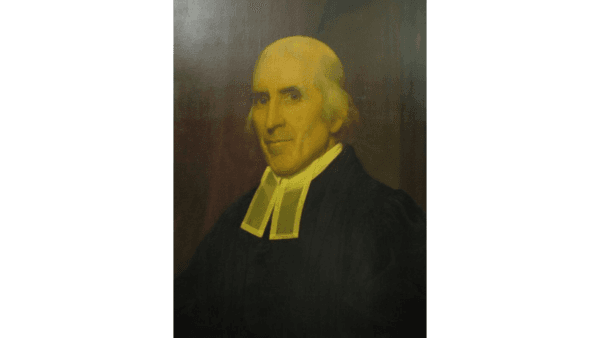
Jedidiah Morse: Father of American Geography
In this installment of ‘Profiles in History,’ we meet a minister who possessed a keen interest in geography and a concern about Christian liberalism.
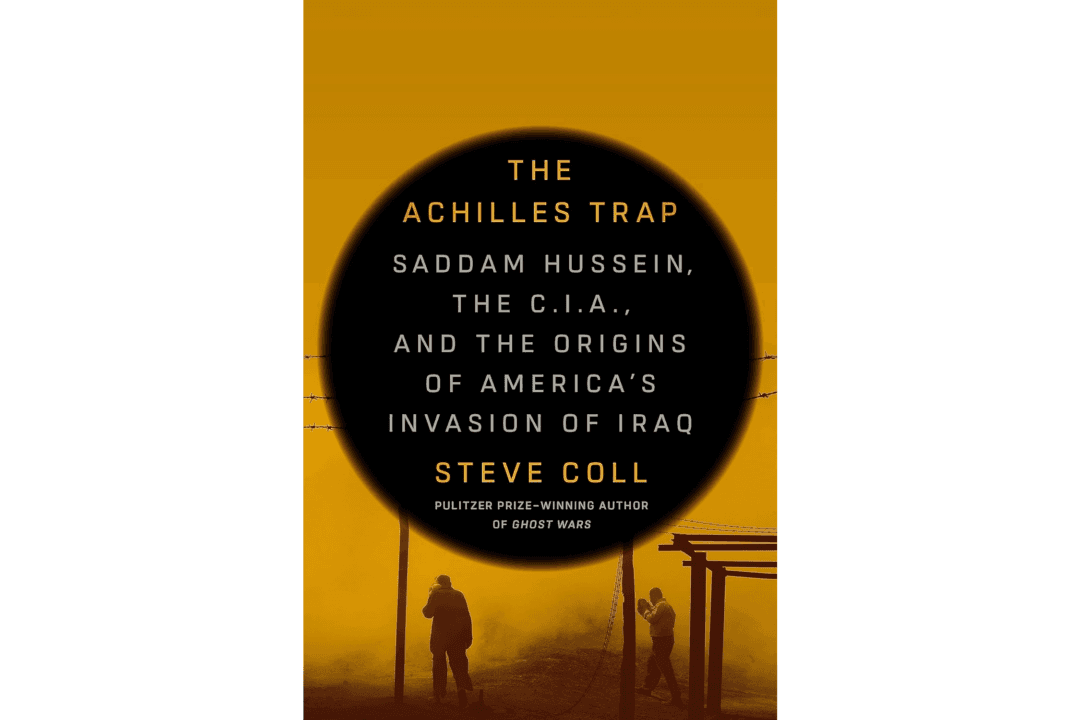
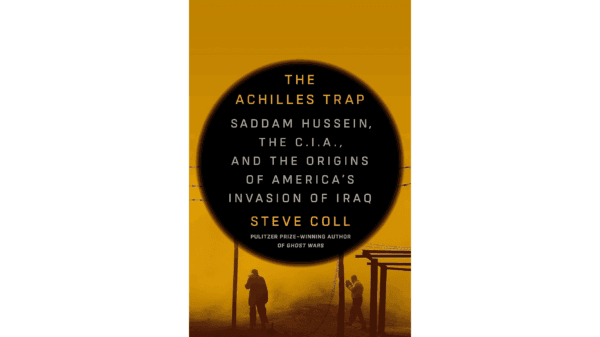
How the US–Iraq Relationship Devolved Into War
Decades of animosity swirl in Steve Coll’s ‘The Achilles Trap: Saddam Hussein, the C.I.A., and the Origins of America’s Invasion of Iraq.'
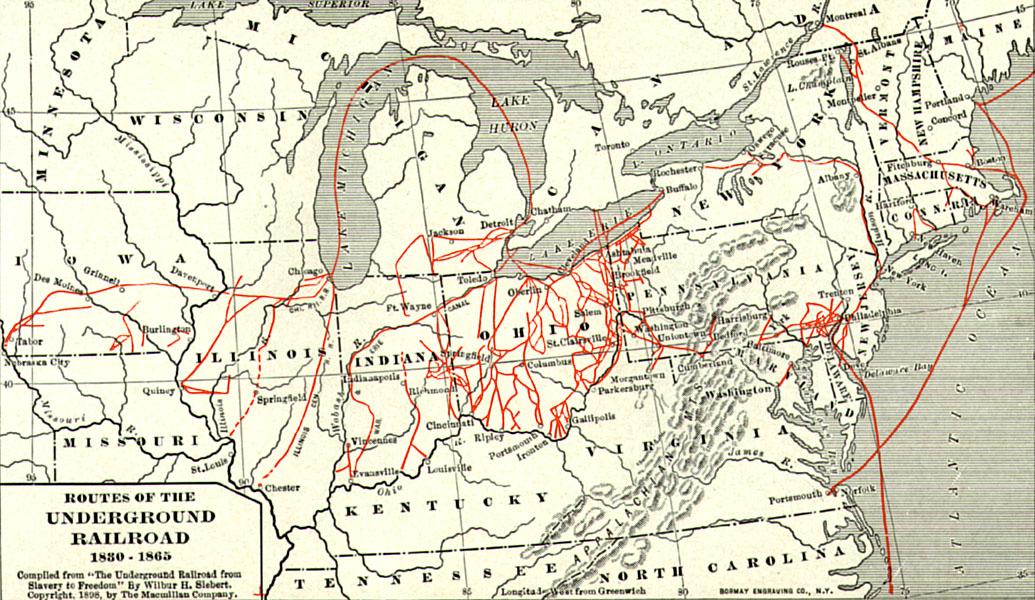
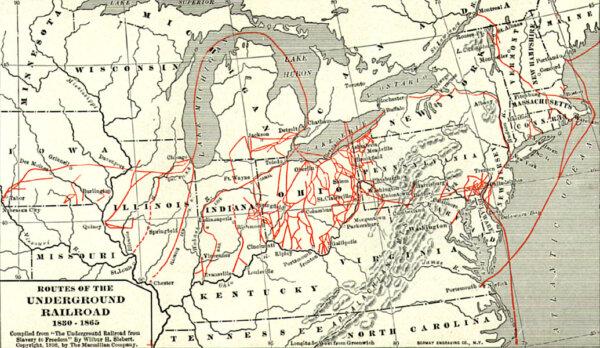
Important Players in a Divided Nation
Sons of the North, including young Spencer Kellogg, gave their all for the fight against slavery during the Civil War.

Morality and Opera: A Traditional Message of Good Versus Evil
In this first installment of ‘A Modern Look at Opera,’ we are introduced to the strong moral messages in this classical performing art.

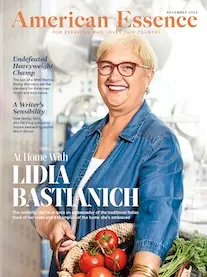
You Need a Kitchen Assistant
Your slow cooker can help you prepare a meal for less that two cents an hour.

These Texas Airports Have Flight Cancellation Rates That Place Them Among the Highest in the Country, Study Finds
Airports across the country have made the list with New York and New Jersery placing in the top 3.

Rocky Mountaineer Train Launches Summer Season Promising Spectacular Views
Rocky Mountaineer has four routes that will take passengers through Western Canada and the American Southwest.

After 5 Years of Closure, ‘Glamping’ Back Again in Yosemite National Park
Camping hopefuls can now enter a lottery to experience three of the five available campsites.
These Texas Airports Have Flight Cancellation Rates That Place Them Among the Highest in the Country, Study Finds
Airports across the country have made the list with New York and New Jersery placing in the top 3.







































![[PREMIERING APR 26, 7:00PM ET] Hope for Israel | Special Report](/_next/image?url=https%3A%2F%2Fimg.theepochtimes.com%2Fassets%2Fthemes%2Feet%2Fimages%2FEET_default_700x420.jpg&w=1200&q=75)







































































![[PREMIERING 4/25, 9PM ET] Up to 5 Years in Prison for Possession of a Meme? Hermann Kelly on Ireland’s New Hate Speech Bill](/_next/image?url=https%3A%2F%2Fimg.theepochtimes.com%2Fassets%2Fuploads%2F2024%2F04%2F25%2Fid5637157-240424-ATL_Hermann-Kelly_HD_TN-600x338.jpeg&w=1200&q=75)










![[LIVE Q&A 04/25 at 10:30AM ET] Why Is Australia Going After Elon Musk?](/_next/image?url=https%3A%2F%2Fimg.theepochtimes.com%2Fassets%2Fuploads%2F2024%2F04%2F24%2Fid5636785-CR-TN_REC_0425-600x338.jpg&w=1200&q=75)