SPECIAL COVERAGE
Read More
Read More
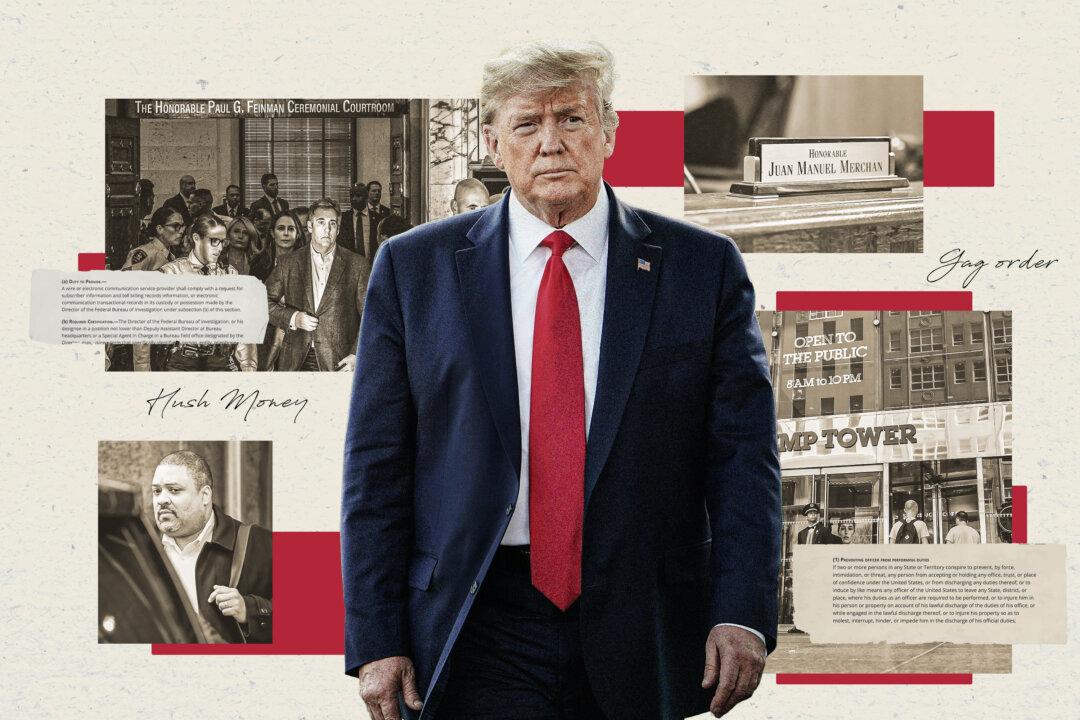
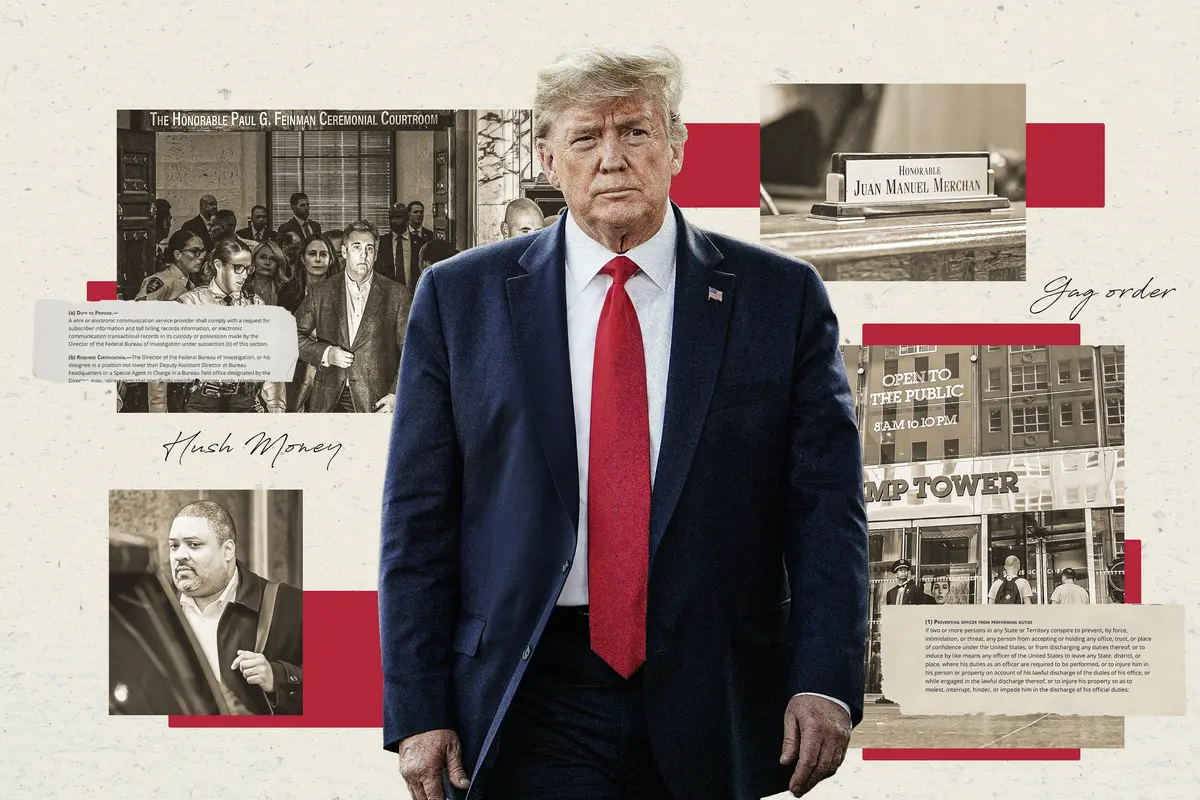
Group of Potential Jurors Dismissed on First Day of Trump Criminal Trial
Manhattan prosecutors accuse Trump of falsifying business records in making a hush money payment to adult actress Stormy Daniels.
Group of Potential Jurors Dismissed on First Day of Trump Criminal Trial
Manhattan prosecutors accuse Trump of falsifying business records in making a hush money payment to adult actress Stormy Daniels.
Top Premium Reads
Top Stories
Most Read
‘China Press’ Has Deep Ties to the CCP but Isn’t Registered as a Foreign Agent
The US-based newspaper targets Chinese immigrants with Chinese Communist Party propaganda.
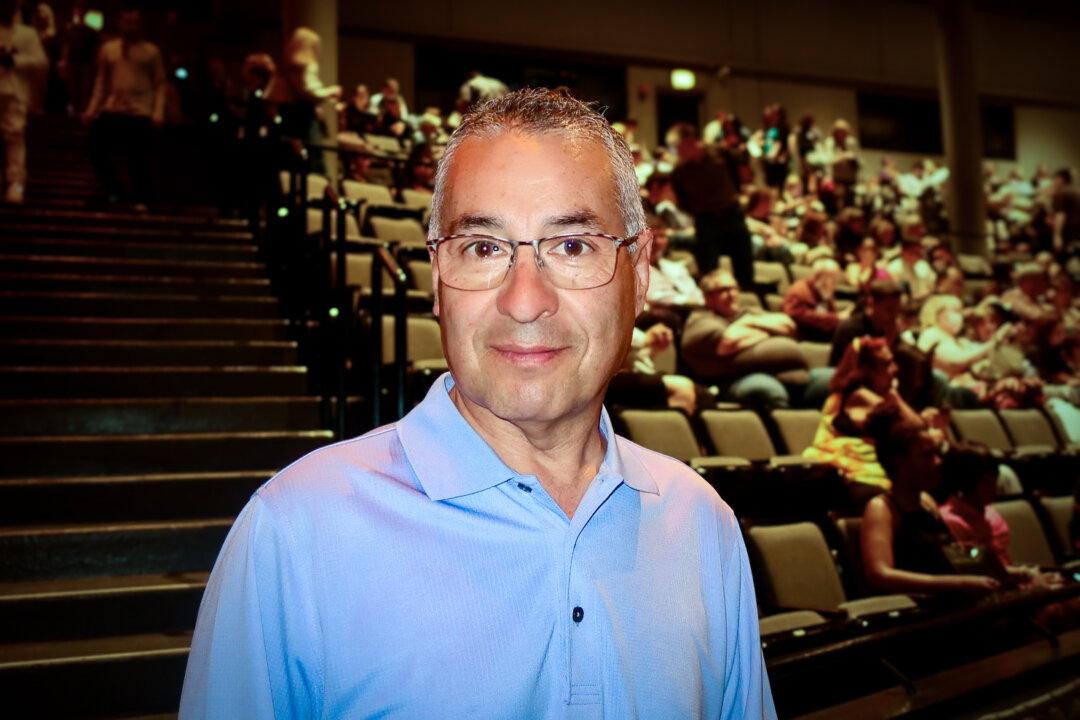
Confluence 2024 Focuses on Building ‘Resilient Communities’
More self-reliance and less dependance on government were dominant themes of the yearly event.
Elon Musk Considering Paywall for New X Users to Fight the Bots
The entrepreneur said this might be the only way to combat bots on the platform.
CCP’s Persecution of Faith Group Sparks ‘Single Largest Whistleblower’ Movement: Documentary
‘We’re dealing with a party that not only runs an entire country but has extensive operations around the world.’
Johnson Plans to Bring Separate Ukraine, Israel, Foreign Aid Bills to Floor
The four part plan will include three separate financial assistance packages: one for Ukraine, one for Israel, and one for Taiwan.
Chinese TikTok’s Campaign of Using Influencers to Target Lawmakers Could Backfire
‘Our intention is for TikTok to continue to operate, but not under the control of the Chinese Communist Party,’ said Rep. Raja Krishnamoorthi.
House Doubles Down on FISA Authorization, Rejects Motion to Reconsider
Lawmakers have tabled an effort to amend FISA for greater civil liberty protections. The Act has been reauthorized for April 19.
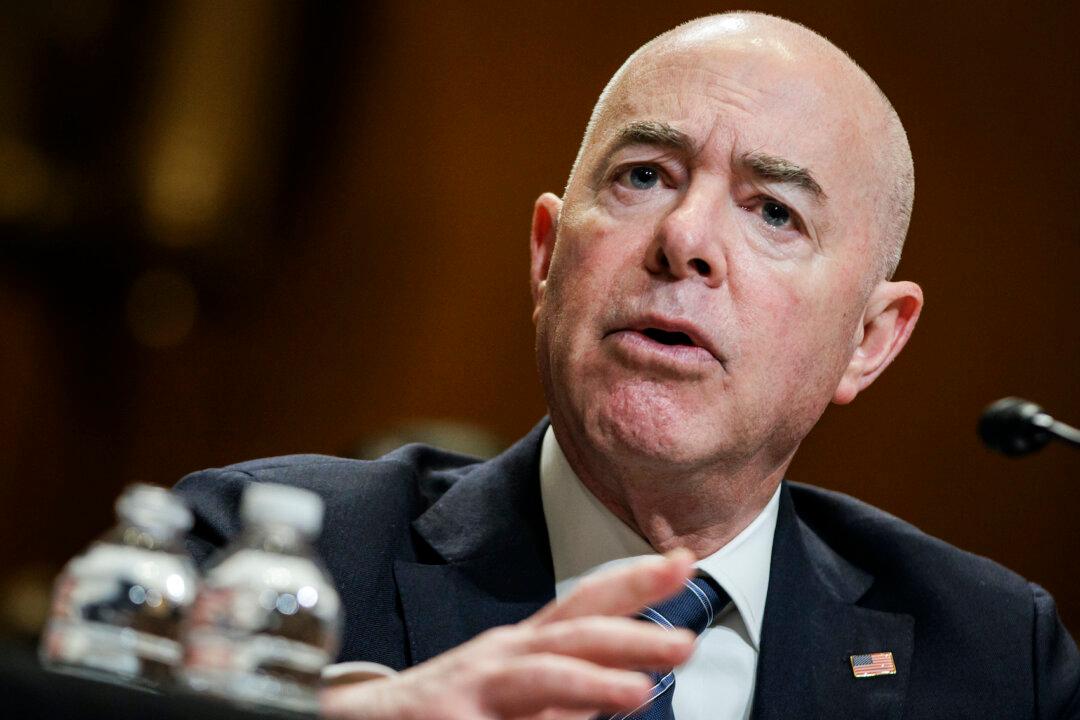
‘Nonsense’: White House Shuts Down Idea Iran Warned US of Attack on Israel
‘This attack was defeated thanks to our preparations, to a coalition of committed partners, and to Israel’s remarkable defensive systems,’ John Kirby said.
Supreme Court to Hear Landmark J6 Appeal That Could Impact Trump Case
The case addresses a portion of the Sarbanes-Oxley Act of 2002 pertaining to the obstruction of official proceedings.
Trump Makes History as Trial Begins in New York
The case will take President Trump off the campaign trail for an expected six to eight weeks.
Supreme Court Curbs Power of Local Governments to Impose Permitting Fees
The unanimous decision finds a California county’s development fees unconstitutional.
Supreme Court Rejects Appeal by Pro-Trump Lawyer Sidney Powell to Review 2020 Election Lawsuit Sanctions
‘This case is not moot,’ Ms. Powell said in a legal brief. ‘That finding is unsupportable factually and legally.’
More Than 50 Jurors Dismissed on First Day of Trump ‘Hush-Money’ Trial
It has been estimated that more than half left due to a judge’s question about impartiality.
Elon Musk Calls Trump Trial ‘Obviously a Corruption of the Law’
‘This case is obviously a corruption of the law,’ Mr. Musk said. ‘Lawfare.’

‘The Rose of Tralee’: A Woman’s Virtue Celebrated
An Irish town’s famous love story and beloved folk song inspires a yearly festival honoring beauty and virtue.
‘The Rose of Tralee’: A Woman’s Virtue Celebrated
An Irish town’s famous love story and beloved folk song inspires a yearly festival honoring beauty and virtue.
Epoch Readers’ Stories
Wisdom From a Retired Cowboy Artist
I have lived the life of the sculptures I have made.
Section 3 of 14th Amendment Not Applicable for Ruling Trump out of 2024
I don’t believe that Section 3 of 14th Amendment is self-executive and therefore can not be applied directly by the court.
Inspired Stories
Empower the World with Your Story: Share Love, Inspiration, and Hope with Millions
Special Coverage
Special Coverage
Against All Odds: How a World-Renowned Doctor Uses Science and Faith to Treat Blindness
For Dr. Ming Wang, science and faith play crucial roles in helping blind people see.
Against All Odds: How a World-Renowned Doctor Uses Science and Faith to Treat Blindness
For Dr. Ming Wang, science and faith play crucial roles in helping blind people see.

The Impact and Legacy of Romantic Opera
In this installment of ‘Opera Through the Ages,’ we learn about musical storytelling that expressed powerful emotions in the 19th century.
‘Seveneves: A Novel’: A Catastrophe Shakes Up Humanity
Neal Stephenson explores the challenge of extinction in this sci-fi novel.
‘The Professionals’: A South-of-the-Border Buddy Adventure
Burt Lancaster plays a rogue in this ‘save the damsel in distress’ feature.
‘Knox Goes Away’: A Morally Ambiguous ‘Bourne Identity’
Jason Bourne was a CIA patriot with a dangerous mission. Knox is a morally questionable hitman. Both have no memory. Top-shelf storytelling by Michael Keaton.
The War That Almost Happened
A new novel about the Cuban Missile Crisis offers some lessons for today’s world leaders.

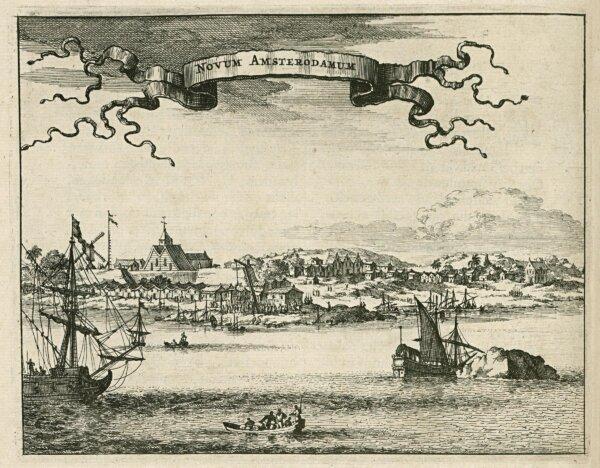
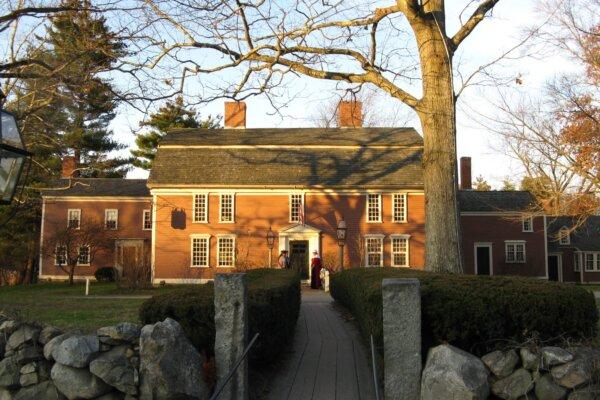
Dutch Subversion, British Aggression, the First US Ambassador
In ‘This Week in History,’ the Dutch and English battled for land, a revolution broke out, and a headstrong statesman became the first U.S. ambassador.

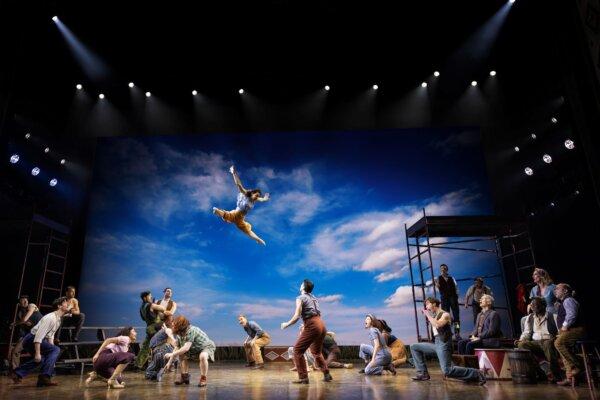
‘Water for Elephants’: Circus Acts, Love, and Adventure
The Broadway version carries more than water for Sara Gruen’s bestselling novel.

The Impact and Legacy of Romantic Opera
In this installment of ‘Opera Through the Ages,’ we learn about musical storytelling that expressed powerful emotions in the 19th century.

Skillet Dinner Delivers on Flavor, Easy Cleanup
This one skillet dish builds layers of flavor while cooking.

Yurt Overnights Returning to Colorado State Park After Controversial Pause
Yurts were traditionally used by nomads in Mongolia, Siberia, and Turkey.
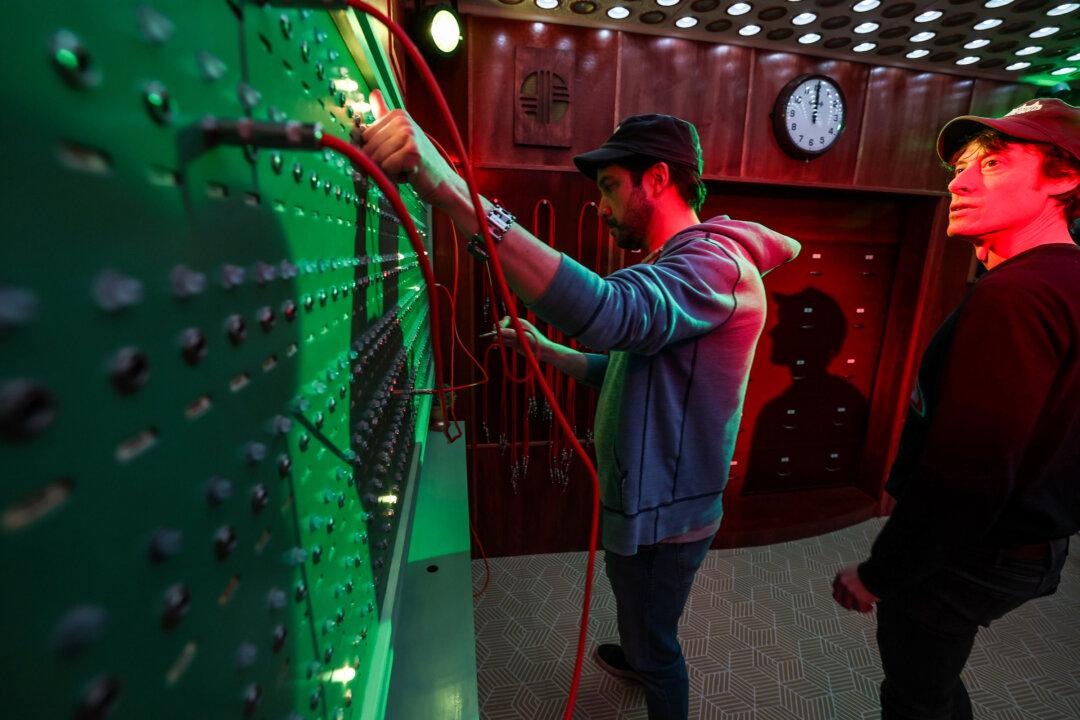
This LA Escape Room Explores Corporate Greed—and Shows How Corruptible You Really Are
An escape room is not mere entertainment but can, in fact, be experienced as a work of narrative art.

Will Big Sur Headaches Never End? Another Partial Road Collapse Adds to the Coastal Mecca’s Woes
Closing the highway is costing restaurants and other businesses millions.
Yurt Overnights Returning to Colorado State Park After Controversial Pause
Yurts were traditionally used by nomads in Mongolia, Siberia, and Turkey.

















































































































![[LIVE Q&A 04/16 at 10:30AM ET] Trump Taken Off Campaign Trail to Stand Trial in New York](/_next/image?url=https%3A%2F%2Fimg.theepochtimes.com%2Fassets%2Fuploads%2F2024%2F04%2F15%2Fid5629991-CR-TN_REC_0416-600x338.jpg&w=1200&q=75)